Microsoft has issued a security advisory, and confirmed reports that a zero-day vulnerability in Internet Explorer has been used in targeted attacks. One such attack was reported last week, when a drive-by download attack on the website maintained by the Council on Foreign Relations (CFR), leveraged the vulnerability to spread malware.
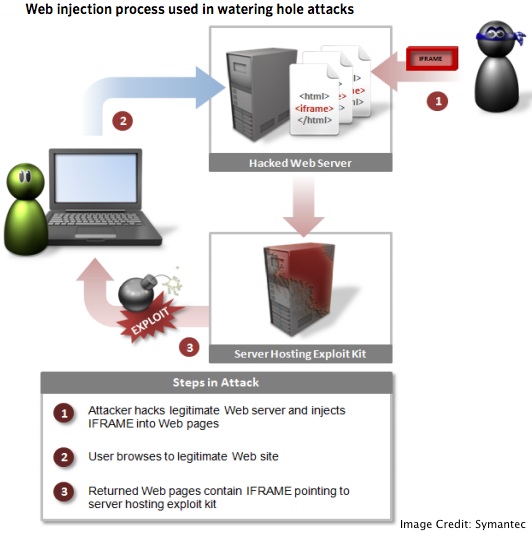
In the case of the CFR incident, the vulnerability was exploited in a type of attack known as a “watering hole” attack, a semi-targeted attack used to compromise a wide number of victims by infecting a site often visited by a target audience, such as government-related sites, financial services, and organizations working to push democracy.
According to research from FireEye, the vulnerability in Internet Explorer is targeted by Adobe Flash, but they have withheld full technical details.
“In the meantime, the initial JavaScript hosting the exploit has some interesting features. To start, it appears the JavaScript only served the exploit to browsers whose operating system language was either English (U.S.), Chinese (China), Chinese (Taiwan), Japanese, Korean, or Russian,” FireEye explained.
Microsoft published an advisory on the zero-day attacks, and warned users of Internet Explorer versions 6,7,8 that they are vulnerable, urging them to apply updates as soon as possible. Internet Explorer versions 9 and 10, are not vulnerable to this latest attack. “The vulnerability is a remote code execution vulnerability that exists in the way that Internet Explorer accesses an object in memory that has been deleted or has not been properly allocated,” Microsoft’s advisory explains.
“An attacker could host a specially crafted website that is designed to exploit this vulnerability through Internet Explorer and then convince a user to view the website,” the advisory continued. “On completion of this investigation, Microsoft will take the appropriate action to protect our customers, which may include providing a solution through our monthly security update release process, or an out-of-cycle security update, depending on customer needs.”
The conservative blog Washington Free Beacon first reported the attacks targeting the vulnerability on the CFR website last Thursday, citing sources that blamed China for the malicious code. While that report had no solid proof, it was the first instance of the flaw being leveraged on a large scale. According to an email sent to CFR members, the source of the drive-by attack has been cleaned up, though an internal investigation is ongoing.
Earlier this year, Symantec noted that watering hole attacks were on the rise, and warned stakeholders in various industries that these types attacks are not likely to subside anytime soon, adding that organizations should be on the defense moving forward.
Related: IE Zero-Day Attacks Tied to Notorious Elderwood Gang, Symantec Says














