Back in early 2010, Google announced it had been a victim of a persistent and sophisticated attack conducted over a sustained period of time. According to Google, the attackers behind “Operation Aurora” were from China and had the backing of the Chinese government.
On Friday, Symantec released a report claiming the Aurora attackers used the same methods to target more than 1,000 in various industry sectors and non-governmental organizations in recent years. The group, dubbed the “Elderwood gang” by Symantec for a parameter used in the attack source code, used a combination of zero-day vulnerabilities and compromised Web servers to launch the attacks, according to a research report released by Symantec Security Response.
 The Aurora attackers utilized a Trojan called Hydraq which exploited a then-zero-day vulnerability in Internet Explorer to infect machines and steal information, Google said at the time. Symantec researchers said at least two Adobe Flash zero-day vulnerabilities were exploited in a manner similar to how Hydraq exploited IE in the latest attacks by the Elderwood gang.
The Aurora attackers utilized a Trojan called Hydraq which exploited a then-zero-day vulnerability in Internet Explorer to infect machines and steal information, Google said at the time. Symantec researchers said at least two Adobe Flash zero-day vulnerabilities were exploited in a manner similar to how Hydraq exploited IE in the latest attacks by the Elderwood gang.
“We believe the Hydraq attack and the recent attacks that exploit the vulnerabilities outlined above are linked,” Symantec researchers wrote in the report.
Symantec identified eight zero-day vulnerabilities used by the Elderwood gang, including two flaws in IE, one in Microsoft XML Core Services, and five Adobe Flash Player issues. The attacks involved tricking victims into visiting a compromised Website, which would then download one of the exploits to give access to the victim’s computer and network. Once in, the perpetrators could steal documents and monitor network activity and communications.
While there were some commonalities in the attack infrastructure and scripts used, RSA researchers, who had independently been tracking the same attacks over the summer, were not convinced links existed between the Elderwood gang and the Aurora attackers, Alex Cox, principle security researcher for the advanced threat research team at RSA, told SecurityWeek. RSA didn’t work with Symantec on this analysis, so it is possible Symantec researchers saw something they didn’t disclose in the report and that RSA never encountered, but based on RSA’s own analysis, Symantec may have made connections where none exists, he said.
“We don’t agree with Symantec’s assertion,” Cox said.
The attack codes and the malware packer used by the Elderwood gang are all easy to find online, Gragido said. Any similarities between the Elderwood gang and the Aurora attacks may be explained by the fact that both groups used readily available components, such as the malware packer used in Aurora’s Hydraq.
RSA researchers analyzed the attacks that occurred between June and July this year, and found the perpetrators a “watering hole” technique to compromise a large number of victims. The watering hole in this case is a third-party Website that many people visit, such as local government-related sites, financial services, and organizations working to establish democracy abroad, Cox said. The sites that had been compromised all shared one thing in common: they were all based in Washington, DC.
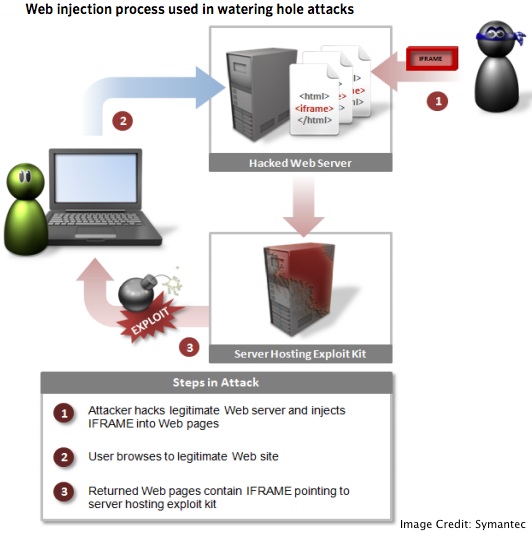
Attackers compromised these Web servers and modified the sites to automatically redirect the victim to another site which actually hosts the exploit code for a particular vulnerability, according to Symantec’s description of the attack. The initial compromise varies by the site, as in exploiting a live vulnerability on a Web site or using spear phishing techniques. Either way, visitors to these watering holes are compromised when they land on the site and the exploit is triggered.
According to Symantec, watering hole attacks are on the rise.

This attack method is a little unusual for nation-state actors to employ, as they don’t necessarily need to cast such a wide net, Gragido said. Traditionally, these attackers prefer much more targeted campaigns, but this technique may have been successful in this case because it was useful in gathering larger amounts of data.
There is not enough proof that China was behind the Elderwood gang. The attack package contained the Chinese language version of the malware, but it is still possible that the group making decisions were not based in China at all, Cox noted. In fact, the fact that the malware, exploit kit, and the script contained Chinese meant the developer at least knew how to read the language, he said
The majority of the victims were based in the United States, and the attackers’ goal was to gather intelligence and steal intellectual property, Symantec said.
Many of the attacks involved supply-chain companies, which may have been compromised in order to gain a foothold in other companies that were the actual targets, Symantec said.
“Although we have not conclusively established a connection between the most recent exploits and those used in attacks in 2011, there are similarities,” Symantec’s admitted in its report. “Apart from the technical features in common, as mentioned previously (URL encoding), there is a noticeable similarity in the timing of the attacks and the types of vulnerabilities used between the 2012 and 2011 attacks.”
Finally, Symantec warned stakeholders in various industries that these types attacks are not likely to subside anytime soon, and that organizations should be on the defense moving forward.
“Any manufacturers who are in the defense supply chain need to be wary of attacks emanating from subsidiaries, business partners, and associated companies,” the report warned.
“Companies and individuals should prepare themselves for a new round of attacks in 2013 utilizing both Adobe Flash and Internet Explorer zero-day exploits,” they said. “This is particularly the case for companies who have been compromised in the past and managed to evict the attackers. The knowledge that the attackers gained in their previous compromise will assist them in any future attacks.”















