Kaspersky Lab has expanded its small and medium-sized business (SMB) offering with a new cloud-based product designed to provide an extra layer of security for the Exchange Online email service in Microsoft Office 365.
The new product, Kaspersky Security for Microsoft Office 365, is designed to protect users against malware, phishing, spam, and other email-borne threats.
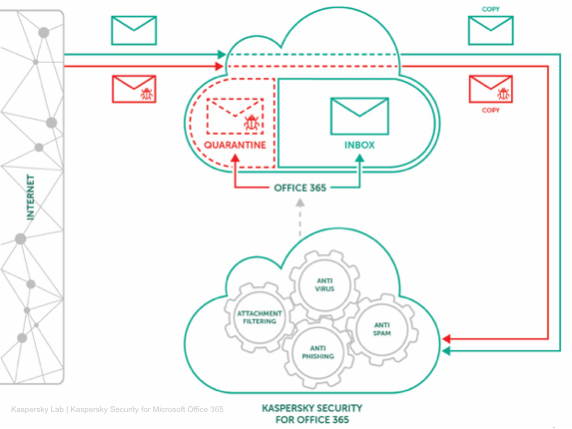
Exchange Online includes built-in anti-malware and anti-spam features, but Kaspersky says its own product – part of the company’s Business Hub offering – works in conjunction with Microsoft’s protections and offers native integration.
Kaspersky says its product relies on various security technologies, including machine learning-based detection, an anti-phishing engine that uses neural networks, sandboxing, attachment filtering mechanisms, and data from the company’s threat intelligence network.
The new product analyzes incoming emails and places suspicious messages in quarantine. Administrators are informed of the potential threats via a central console shared with the Kaspersky Endpoint Security Cloud product. The console allows customers to view each potentially malicious email and restore them in case of false positives.
According to the security firm, Kaspersky Security for Microsoft Office 365 is capable of recognizing if a file attached to an email is the type it claims to be, and it can detect malicious macros hidden in harmless-looking Office documents.
Since there has been a lot of debate recently on the implications of the physical location of data stored in the cloud, Kaspersky allows users to specify which data center they want to use for processing emails.
Furthermore, given the recent controversy regarding the company uploading sensitive files from an NSA contractor’s computer to its own servers, Kaspersky has highlighted that the new product does not upload any files to its systems. Instead, quarantined emails are stored in the customer’s Exchange Online account.
Related: Kaspersky Releases Open Source Digital Forensics Tool
Related: Peace Breaks Out Between Microsoft and Kaspersky Lab















