Intel patched over 230 vulnerabilities in its products last year, but less than a dozen impacted its processors, according to the company’s 2019 Product Security Report.
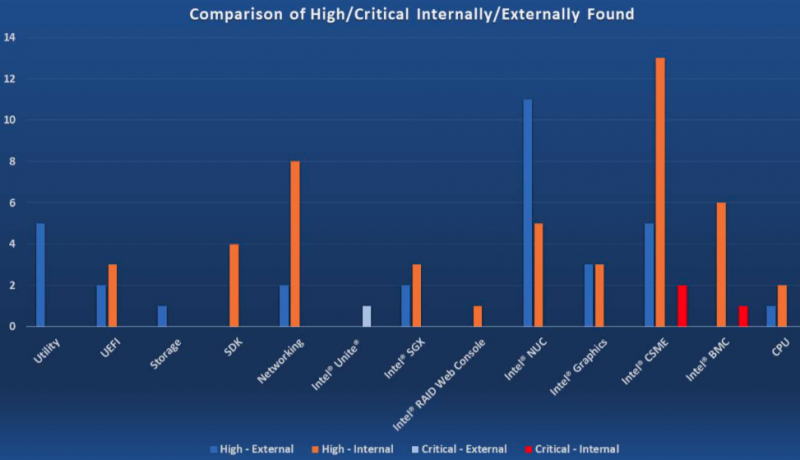
Intel said it learned of 236 vulnerabilities in 2019, including 144 discovered internally by its employees. Internally discovered issues included 61% of the vulnerabilities rated high severity, and 75% of those rated critical. In total, 4 flaws were rated critical and 81 were classified as high severity.
Three quarters of the vulnerabilities reported by external researchers were submitted through the company’s bug bounty program.
“Combining Bug Bounty and internally found vulnerabilities, the data shows that 91% of the issues addressed are the direct result of Intel’s investment in product assurance,” the company wrote in its report.
The chip maker says only 11 vulnerabilities affected its CPUs, with an average yearly CVSS score of 5.02. This includes the MDS flaws named ZombieLoad, Fallout and RIDL.
“As acknowledged by security researchers and industry experts, side-channel issues are difficult to exploit and often require a level of access to the target system that would afford would be attackers more efficient and reliable methods of obtaining and exfiltrating information,” Intel explained.
Of the 236 vulnerabilities found last year in the company’s products, 112 affected software, 59 affected firmware and 13 impacted hardware. In the case of 52 vulnerabilities, patching required both software and firmware updates.
Intel says it has found no evidence to suggest that any of the vulnerabilities patched last year have been exploited in attacks.
Earlier this week, the company announced four new security capabilities and provided further information on its previously-announced Compute Lifecycle Assurance supply chain transparency initiative.
Related: Intel Patches Serious Vulnerability in Processor Diagnostic Tool
Related: Intel Patches Privilege Escalation Flaw in Rapid Storage Technology
Related: Lawsuits Filed Against Intel Over CPU Vulnerabilities














