Major industrial control system (ICS) vendors and other types of organizations have been targeted in a cyberespionage campaign that appears to focus on renewable energy.
The campaign, which started in at least 2019 and is ongoing, was analyzed by William Thomas, security researcher at Curated Intelligence. While the findings are limited due to the analysis relying solely on OSINT techniques, they are nevertheless interesting.
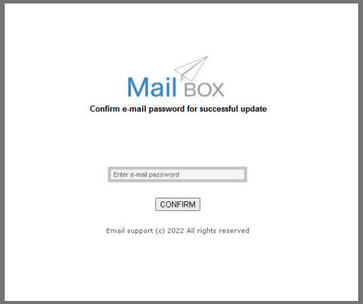
Using public sandbox submissions and passive DNS scans, Thomas identified tens of users apparently targeted in a phishing campaign that leveraged a basic “Mail Box” phishing kit to harvest usernames and passwords. The phishing pages are hosted on dedicated domains, as well as on compromised websites.
Based on the targeted email addresses, the operation is aimed at the employees of organizations in various sectors, but the focus appears to be on renewable energy. Targets include employees of ICS vendors such as Honeywell and Schneider Electric, Chinese communications giant Huawei, and Chinese chipmaker HiSilicon.
The phishing was also aimed at several universities in the United States, including the University of Wisconsin, California State University, and Utah State University.
NGOs and government organizations have also been targeted, including the California Air Resources Board, the Morris County Municipal Utilities Authority, the Taiwan Forestry Research Institute, and the Carbon Disclosure Program.
Other victims include the Kardzhali power plant and the CEZ Electro electricity supplier in Bulgaria, Romanian telecoms company Telekom, and Italian plastic recycling firm Sorema. Some of the infrastructure used in this campaign was also used back in 2019 to target multiple banks in Bulgaria.
While attribution is difficult, the researcher found links to two known activity clusters — one previously attributed to the threat group known as APT28 and Fancy Bear, which is believed to be Russian intelligence, and one attributed to Konni, which has been tied to the North Korean government. However, there is insufficient evidence to definitively link the phishing attacks to either of these threat actors.
Learn more about ICS threats at SecurityWeek’s ICS Cyber Security Conference
“Attribution using these campaign artefacts and OSINT reports alone was not possible,” Thomas wrote in a blog post. “However, it can be inferred that the adversary behind these attempts appears to be interested in Bulgaria, for starters, plus critical infrastructure, renewable energy, environmental protection agencies, and recycling technology.”
The researcher added, “Supplemental targets such as ICS/OT organisations and educational institutions would complement this intelligence gathering campaign, if access could be obtained at these entities. From this it could be suggested that the adversary behind this campaign is potentially a major source of fossil fuels and is doing research on the renewable energy sector as a threat to its income.”
Thomas has made available indicators of compromise (IoC) and other technical information on this campaign.
Related: Thousands of Industrial Systems Targeted With New ‘PseudoManuscrypt’ Spyware
Related: ‘WildPressure’ Campaign Targets Industrial Sector in Middle East
Related: Cybercriminals Target Industrial Organizations in Information Theft Campaign














