A total of 15 threat groups have been observed targeting industrial organizations, according to industrial cybersecurity firm Dragos.
Dragos on Wednesday released its ICS Cybersecurity Year in Review report for 2020, which covers the industrial control systems (ICS) threat landscape and vulnerabilities disclosed last year. It also shares insights from the lessons learned by Dragos as a result of its work in 2020, and provides recommendations for industrial organizations on securing their networks.
In 2018, Dragos reported seeing five groups that had either attacked ICS directly or had shown an interest in gathering information on these types of systems. The next year, the company reported that the number had grown to nine, and now there are a total of 15 activity groups.
Dragos said it added four new groups to the list in 2020. These threat actors have shown an interest in targeting operational technology (OT) systems. In addition, the previously described 11 groups remained active.
The company told SecurityWeek that the newly added groups “have the potential to disrupt control systems, but have not been seen exclusively targeting control systems.”
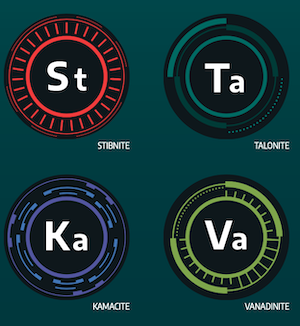 One of the new groups is tracked by Dragos as STIBNITE and it has been observed targeting electric energy companies — specifically wind turbines — in Azerbaijan. While there is an ongoing conflict between Armenia and Azerbaijan, the cybersecurity firm said there is “only a loose correlation between the conflict and STIBNITE operations, and the Dragos team is not making an assessment on who may be responsible for the targeting.”
One of the new groups is tracked by Dragos as STIBNITE and it has been observed targeting electric energy companies — specifically wind turbines — in Azerbaijan. While there is an ongoing conflict between Armenia and Azerbaijan, the cybersecurity firm said there is “only a loose correlation between the conflict and STIBNITE operations, and the Dragos team is not making an assessment on who may be responsible for the targeting.”
STIBNITE, which has been seen using PoetRAT malware to gather information from victims, may have targeted the supplier and maintainer of the wind farms, which are based in Ukraine.
Another new group is tracked by Dragos as VANADINITE, which has been observed targeting the energy, manufacturing and transportation sectors in North America, Asia, Europe and Australia. The hackers have focused on harvesting information, including related to ICS processes and design, which experts believe could enable its sponsor to develop ICS-targeting capabilities.
Dragos believes VANADINITE could be behind the ransomware known as ColdLock, which has been used to target Taiwan, including state-owned industrial companies whose operations were indirectly disrupted by the ransomware.
VANADINITE has been linked to Winnti — which has been around for over a decade and is believed to have Chinese origins — and a Winnti-related activity group tracked as LEAD.
Learn More About Threats to Industrial Systems at SecurityWeek’s ICS Cyber Security Conference and SecurityWeek’s Security Summits Virtual Event Series
The third new group has been named TALONITE and it appears to focus on initial access to organizations in the U.S. electric sector. The hackers have been conducting phishing campaigns that leverage power grid-related themes. They have been known for the use of malware such as LookBack, a remote access trojan (RAT) that emerged in 2019 when it was used to target U.S. utilities, and FlowCloud, a RAT analyzed by researchers in 2020.
Dragos also started tracking a threat group dubbed KAMACITE, which also targeted U.S. energy companies. KAMACITE’s operations have overlapped with the activities of Sandworm (ELECTRUM), a notorious Russia-linked group that is believed to have launched disruptive attacks against Ukraine’s power grid. Despite the overlaps, Dragos believes KAMACITE is a distinct group that should be tracked separately.
The company believes KAMACITE is an “access-enablement team” that aids other teams specializing in disruptive operations.
“These types of events, where adversaries gain access to ICS networks but do not have the intention of currently disrupting them, are much more common than is publicly reported,” Dragos said. “The threats are learning ICS. Although not every compromise will relate to an impact today, many may inform the attacks of the future.”
It added, “Threats are growing at a rate three times faster than they are going dormant. This is likely due to the increased investment made by adversaries in targeting ICS over the last five to 10 years, and whose investment will continue to accelerate the ICS threat environment.”
Related: More Threat Groups Target Electric Utilities in North America
Related: Manufacturing Sector Targeted by Five ICS-Focused Threat Groups
Related: Over 400 ICS Vulnerabilities Disclosed in 2019: Report













