WikiLeaks has published a document detailing “Elsa,” a tool allegedly used by the U.S. Central Intelligence Agency (CIA) to track people’s locations via their laptop’s Wi-Fi.
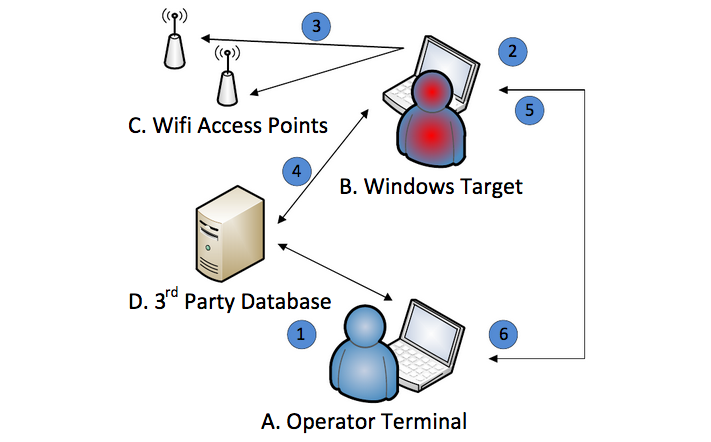
According to its developers, Elsa provides geolocation data by recording the details of Wi-Fi access points, including signal strength, in range of the targeted Windows device. The user’s location and movements can be obtained after the data is sent to third-party location services.
Once Elsa is planted on the target’s computer, it monitors nearby Wi-Fi connections even if the device is not connected to the Internet. Once an Internet connection is available, the malware can send the collected Wi-Fi data to a database containing the geographical location of wireless access points.
The document made available by WikiLeaks showed that Elsa leveraged geolocation databases set up by Google and Microsoft.
The data is encrypted and logged, and the malware’s operator can manually retrieve this log by connecting to the infected device.
“The ELSA project allows the customization of the implant to match the target environment and operational objectives like sampling interval, maximum size of the logfile and invocation/persistence method,” WikiLeaks said. “Additional back-end software (again using public geo-location databases from Google and Microsoft) converts unprocessed access point information from exfiltrated logfiles to geo-location data to create a tracking profile of the target device.”
The user manual leaked by WikiLeaks as part of its Vault 7 dump is dated September 2013, which indicates that the tool may have been improved significantly if it’s still maintained by its developer.
Earlier this month, WikiLeaks also published documents detailing tools allegedly used by the CIA to spread malware on a targeted organization’s network (Pandemic), hack routers and access points (Cherry Blossom), and hack air-gapped networks using USB drives (Brutal Kangaroo).
WikiLeaks has also detailed tools designed for replacing legitimate files with malware, hacking Samsung smart TVs and routers, MitM tools, a framework used to make malware attribution and analysis more difficult, and a platform for creating custom malware installers.
Security firms have found links between the tools exposed by Wikileaks and the malware used by a cyber espionage group tracked as “Longhorn” and “The Lamberts.”
















