WikiLeaks published several documents on Thursday detailing a tool allegedly used by the U.S. Central Intelligence Agency (CIA) to hack air-gapped networks through USB drives.
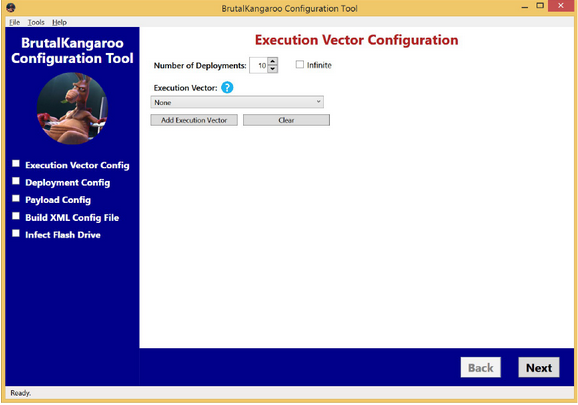
Dubbed “Brutal Kangaroo,” it has been described by its developer as a tool suite designed for targeting closed networks. The infected systems will form a covert network, and the attacker will be able to obtain information and execute arbitrary files.
One component of Brutal Kangaroo is called “Shattered Assurance” and it’s designed to automatically spread the tool to USB drives connected to a device within the targeted organization that was infected remotely via the Internet. Shattered Assurance relies on a tool named “Drifting Deadline” to infect thumb drives.
Once the victim connects the infected drive to an air-gapped network and Brutal Kangaroo is deployed, a component named “Broken Promise” is used to evaluate the harvested data. The last component, dubbed “Shadow,” acts as the primary persistence mechanism and command and control (C&C) server on the closed network.
The documents published by WikiLeaks show that Drifting Deadline and Shattered Assurance replaced two previous tools named “EZCheese” and “Emotional Simian.”
Brutal Kangaroo infects USB drives by exploiting Windows vulnerabilities that allow an attacker to execute arbitrary DLL files using specially crafted shortcut (LNK) files. At least some of the exploits do not require users to actually run the malicious files.
Earlier versions of EZCheese leveraged a Windows vulnerability (CVE-2015-0096) discovered and patched in 2015. The flaw is a newer variant of CVE-2010-2568, which the notorious Stuxnet worm used in attacks aimed at Iran’s nuclear program.
One exploit used in later versions, dubbed “Lachesis” and designed for Windows 7, relies on autorun.inf to execute the malicious file as soon as the thumb drive is plugged in. Another exploit, named “RiverJack” and designed for Windows 7, 8 and 8.1, leverages library-ms functionality.
Microsoft said the vulnerabilities used by these exploits have already been patched in supported versions of Windows, but it’s unclear when. The company this month patched a LNK remote code execution flaw (CVE-2017-8464) that has been actively exploited, but no information has been provided on these attacks.
While the exploits may have been successful in some cases, the Brutal Kangaroo documents show that security products from Symantec, Avira, Avast, Bitdefender and Kaspersky did block at least some functionality and attack vectors.
WikiLeaks has been publishing CIA files, which are part of a leak dubbed “Vault 7,” nearly every week since March 23. The tools exposed by the whistleblower organization include ones designed for replacing legitimate files with malware, hacking Samsung smart TVs and routers, MitM tools, a framework used to make malware attribution and analysis more difficult, and a platform for creating custom malware installers.
Security firms have found links between the tools exposed by Wikileaks and the malware used by a cyber espionage group tracked as “Longhorn” and “The Lamberts.”
Related Reading: Hackers Can Use Scanners to Control Air-Gapped Malware
Related Reading: Router LEDs Allow Data Theft From Air-Gapped Computers















