Oracle informed customers late on Friday that its Database product is affected by a critical vulnerability. Patches have been released and users have been advised to install them as soon as possible.
The security hole, tracked as CVE-2018-3110 with a CVSS score of 9.9, affects Oracle Database 11.2.0.4 and 12.2.0.1 on Windows. Version 12.1.0.2 on Windows and Database running on Unix or Linux are also impacted, but patches for these versions were included in Oracle’s July 2018 CPU.
The vulnerability, present in the Java VM component of Oracle Database Server, can be exploited to take complete control of the product and obtain shell access to the underlying server.
However, the vendor noted that the weakness cannot be exploited remotely without authentication, and that the fix does not apply to client-only installations (i.e. installations that do not have Database Server).
“Easily exploitable vulnerability allows low privileged attacker having Create Session privilege with network access via Oracle Net to compromise Java VM. While the vulnerability is in Java VM, attacks may significantly impact additional products. Successful attacks of this vulnerability can result in takeover of Java VM,” Oracle said in its advisory.
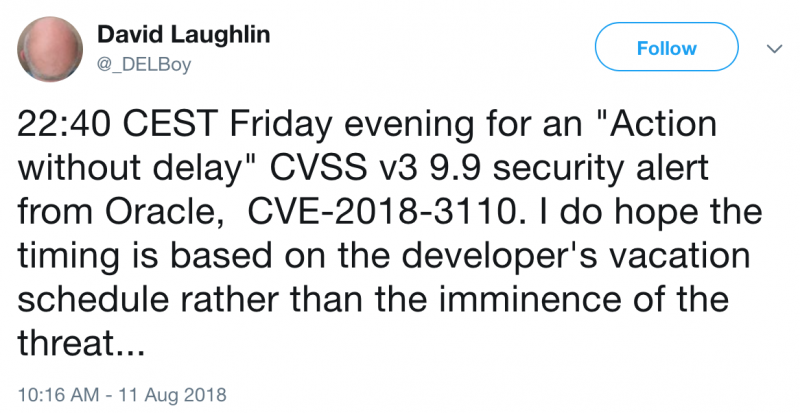
The company “strongly recommends that customers take action without delay” to address CVE-2018-3110, which has led some to wonder if Oracle believes that the risk of exploitation is high.
Related: Oracle Patches New Spectre, Meltdown Vulnerabilities
Related: Hackers Target Poorly Patched Oracle WebLogic Flaw
Related: Recently Patched Oracle WebLogic Flaw Exploited in the Wild














