Cisco has released a software update for its Prime Home remote management and provisioning solution to address a critical authentication bypass vulnerability discovered by the company during internal security testing.
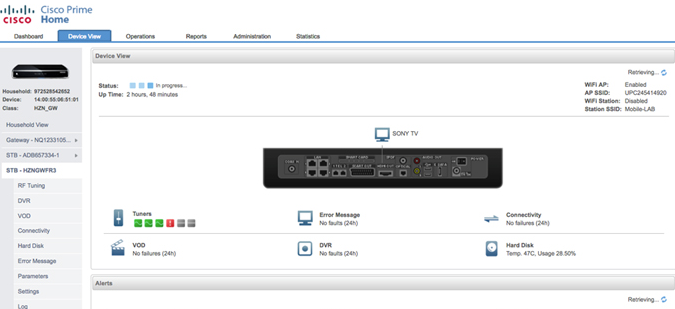
Cisco Prime Home is designed to give Internet service providers (ISPs) visibility into their customers’ home networks, allowing them to easily make configuration changes and software upgrades, and remotely diagnose and troubleshoot problems.
The networking giant discovered that the product’s web-based user interface is affected by a vulnerability that can be remotely exploited by an unauthenticated attacker to bypass authentication and execute any action with administrator privileges.
The flaw, tracked as CVE-2017-3791, is caused by a processing error in the role-based access control (RBAC) of URLs. The security hole can be exploited by sending specially crafted API commands to a particular URL.
The vulnerability affects versions 6.3, 6.4 and 6.5 and it has been addressed with the release of version 6.5.0.1. Workarounds are not available.
Versions 5.2 and earlier are not impacted. However, it’s worth pointing out that, in November 2016, the company informed users about a similar critical authentication bypass vulnerability affecting Cisco Prime versions 5.1.1.6 and earlier and 5.2.2.2 and earlier.
Cisco is only aware of three security holes affecting Cisco Prime Home. The third one, disclosed in September 2016, is a medium severity XML External Entity (XXE) flaw that allows a remote attacker to access information stored on the affected system.
Another critical vulnerability patched recently by Cisco affects the WebEx browser extensions for Chrome, Internet Explorer and Firefox. The vendor has released several updates until it managed to create a proper patch.
Related: Severe Flaws Found in Cisco Management, Security Products
Related: Cisco Patches High Severity Flaws in Several Products















