The US Cybersecurity and Infrastructure Security Agency (CISA) is warning organizations that two vulnerabilities affecting the Mitel MiVoice Connect business communications platform have been exploited in the wild.
CISA has added the flaws to its known exploited vulnerabilities catalog and instructed federal agencies to address them until March 14.
The vulnerabilities, tracked as CVE-2022-41223 and CVE-2022-40765, can be exploited by an attacker with internal access to the targeted organization’s network to execute arbitrary code or commands within the context of the application.
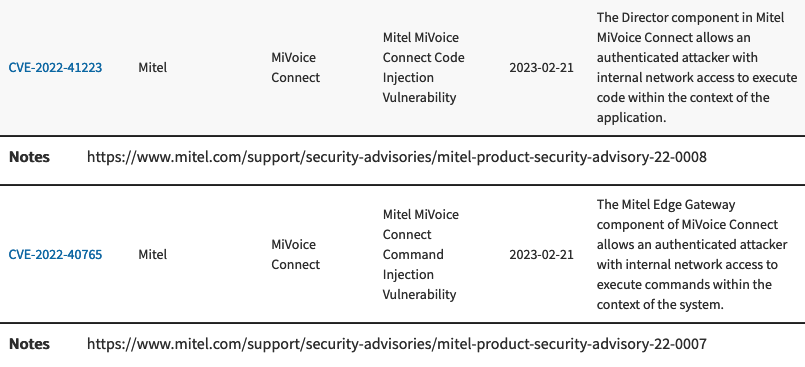
Mitel informed customers about these security holes and the availability of patches in October 2022. A researcher from cybersecurity firm CrowdStrike has been credited by Mitel for reporting the vulnerabilities.
There does not appear to be any public information on the attacks exploiting CVE-2022-41223 and CVE-2022-40765, but CrowdStrike previously saw a Mitel MiVoice Connect flaw being exploited in the wild by cybercriminals.
It’s possible that these newer vulnerabilities are related to the same attacks. SecurityWeek has reached out to CrowdStrike for clarifications and will update this article if the company can share any information.
The Mitel MiVoice Connect vulnerabilities added to CISA’s ‘must-patch’ list have been assigned ‘high risk’ ratings by the vendor, but their exploitation requires authentication. This suggests that threat actors may be exploiting the flaws after they have gained access to the targeted organization’s systems, rather than leveraging them for initial access.
The previous Mitel MiVoice Connect vulnerability that CrowdStrike has seen being exploited in attacks is an unauthenticated remote code execution bug used to gain initial access to the targeted environment.
That vulnerability, tracked as CVE-2022-29499 and rated ‘critical’, has been exploited by ransomware groups, including in the Lorenz ransomware operation.
These are not the only Mitel product vulnerabilities exploited in attacks in the past year. In March 2022, researchers warned that a Mitel flaw tracked as CVE-2022-26143 had been leveraged by threat actors for distributed denial-of-service (DDoS) attacks that employed a new vector with a massive potential amplification ratio.
In addition, Palo Alto Networks warned earlier this month that a Mirai variant called V3G4 has been targeting 13 vulnerabilities — including a Mitel flaw — in an effort to ensnare IoT devices into a botnet. However, that Mitel vulnerability appears to have been around since 2010.
In addition to the Mitel vulnerabilities, CISA has warned organizations about CVE-2022-47986, a recently patched IBM Aspera Faspex bug that has been exploited in the wild.
Related: Exploited Control Web Panel Flaw Added to CISA ‘Must-Patch’ List
Related: CISA Says Two Old JasperReports Vulnerabilities Exploited in Attacks

