While the world of malware creation may be mysterious to many, malicious apps that infect mobile devices are plentiful and easy to create.
Because of readily available tools that enable even a novice developer to create mobile applications that fall on the dark side of the fence, users should be cautious when downloading and installing mobile apps, especially from non-official App Stores.
 Developing Android malware to harvest information is a “trivial” task and possible using readily available tools, Kevin McNamee, security architect and director at Kindsight Security Labs, told SecurityWeek. McNAmee demonstrated how to inject snippets of code into a legitimate Android application that infected a mobile device with malware. The malware, when executed, connected with a remote command-and-control center and transmitted data from the device.
Developing Android malware to harvest information is a “trivial” task and possible using readily available tools, Kevin McNamee, security architect and director at Kindsight Security Labs, told SecurityWeek. McNAmee demonstrated how to inject snippets of code into a legitimate Android application that infected a mobile device with malware. The malware, when executed, connected with a remote command-and-control center and transmitted data from the device.
McNamee downloaded a copy of the Android packager file APK for the popular game Angry Birds and infected it with DroidWhisper, a malicious Java program designed to collect and send phone data to a remote server and execute various commands. Along with the host APK file, all he needed were the regular tools available to any developer on the Android developer site. Criminals not interested in developing their own attack programs can easily obtain actual attack programs online. With the modified game in hand, all that remained was how to distribute it, McNamee said.
“It’s not really our game but we don’t care. We just want to spread the malware,” McNamee said.
He took the Angry Bird APK apart by using the developer tool “apktool” to decompile the entire package. Once done, he could see the source code and directories containing various resources and images. He copied the malicious Java program into the “com” directory. If the source code hadn’t been available, it is possible to inject malware into an app by copying malicious binaries and placing them inside the “res” (resource) or “assets” directories.
Injecting legitimate applications with malicious code was a simple drag-and-drop in the Windows world.
McNamee had a “cheat sheet” of various commands that he needed, transforming the entire process into a cut-and-paste exercise. He opened up the XML file, which defined all the services the app runs when being loaded and user permission, in a text editor. He added a service command with the name of the malicious program inside the command string and several lines that gave the app extra permissions, such as accessing the Internet and sending SMS messages.
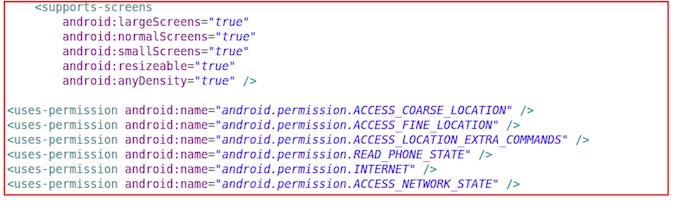
The copied snippets tell the operating system to launch these applications when running the current app. It also tells the OS what permissions the app needs to work.
Users are shown the new permissions when running the modified game, but they are likely to not look at the list or stop to wonder why a game app requires certain permissions, McNamee said.
Malware copied and XML file modified, the next step was to recompile the program with all the changes into a new program. This new build is then distributed, either on an alternative market or as part of a legitimate Google Play offering.
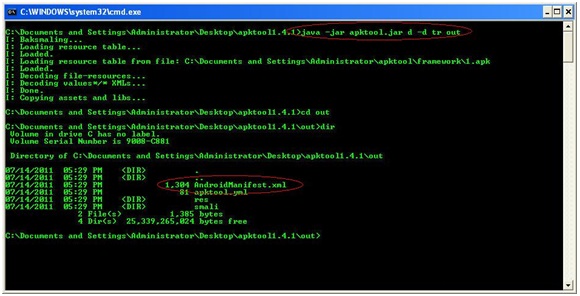
Google has one roadblock, but it’s easy to step over, McNamee said. While Google requires developers to digitally sign the code, there’s no validation in place to examine the signature, he said. McNamee was able to use a private digital signature with the name “Evil Hacker” using the “jarsigner” tool.
“No one checks to see who signed or what was used,” McNamee said.
Once an Android device downloaded the modified app, the device was infected and the program could communicate with the remote C&C server. Executing the game looks completely the same as the real thing and there is no sign of anything running that shouldn’t be. From the C&C server, attackers could see the contact information that had been harvested, geo-location data, and the email address associated with the device, among others. The C&C server can send instructions such as sending spam to all contacts or taking pictures using the device’s camera.
McNamee said he focused on Android devices for his demonstration because Android malware is growing at a far more rapid pace than for other mobile platforms. The open nature of the Android ecosystem, where developers have wider control over what is built and how it interacts with the core operating system, also makes it easier to write successful malware. The lack of tools and the way that iOS apps are often “contained” keeps the Apple platform less at risk.
For criminals, it’s “trivial” to pack malware into existing applications and churn out malicious apps one after another, McNamee said, adding that it’s even a challenge for Google to self-police its marketplace.
Users really have to be on their guard against malicious applications. They need to think about permissions and consider what the app is asking to do, and to be careful where they are downloading apps from. However, these precautions are “not foolproof to the user,” so it’s important to invest in proper security tools to scan the device and identify malicious processes.
















