A cybersecurity enthusiast learned recently that Airbnb accounts can be easily hijacked by creating a new account on the home-rental service with a phone number that in the past belonged to another Airbnb customer.
The security risk posed by recycled phone numbers has been known for years, and the services of several major companies were found to be impacted in the past.
It seems that Airbnb is affected as well, but the company says only a very small number of users are impacted.
A SecurityWeek reader named Maya contacted us recently after her husband was accidentally signed into another user’s account when trying to create an Airbnb account.
After entering his phone number during the account registration process, Maya’s husband received a 4-digit code via SMS that, when entered, resulted in him being logged into the account of the previous owner of his phone number.
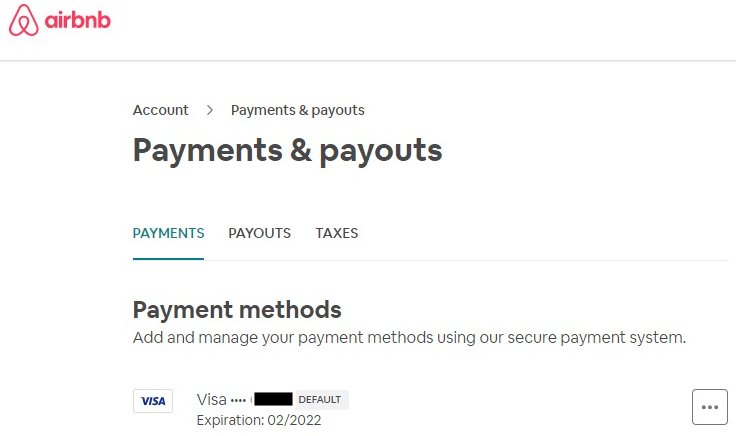
The account they accidentally accessed belonged to a woman from North Carolina and it included her photo, email address, phone number, and other personal information. The account still had a valid payment card attached, making it possible to make a booking on her behalf, using her card.
Maya said she confirmed the issue related to recycled phone numbers by conducting tests with the phone numbers of some of their friends (with their consent). She noted that Airbnb did not inform the new owner of the phone number that the number they were using to sign up for an account was already taken, and it also did not notify the legitimate owner of the account of a potentially suspicious login.
Maya says she works in the tech industry and while she has analyzed the security of her company’s own products, she says she would not describe herself as a security researcher.
Airbnb runs a bug bounty program on HackerOne with rewards of up to $15,000. The company claims to have paid out more than $1 million through its bug bounty program to date, and HackerOne named it one of its top 10 bug bounty programs earlier this year.
Since she is not a professional bug bounty hunter, Maya was not aware of Airbnb’s bug bounty program and she attempted to report her findings through Airbnb’s support channel — she said her only goal was to convince Airbnb to patch the flaw. However, after several attempts to get Airbnb to acknowledge the severity of her findings, she says the issue still hasn’t been addressed — Maya said she last checked on September 22.
Airbnb support staff told Maya to register an account using a different phone number, and claimed that the company ensures every account is secured and can only be accessed by the legitimate account holder. This statement does not seem true given that recycled phone numbers apparently provide a means to repeatedly access other users’ accounts.
“Airbnb support kept telling us the same thing over and over: use a different phone number,” Maya explained. “Without realizing the security issue we raised (although, we’ve been clear with them, and explained ourselves to several people along the way). After all, we did login to another user’s account by accident, and it seems to me they don’t find this as alarming as we do.”
She believes Airbnb should change their login security mechanisms, or at least notify users of suspicious logins in their account.
Airbnb, on the other hand, claimed last week that it had taken action to fix the problem, but it refused to elaborate on the changes it made.
“We’ve developed a resolution for the reported issue involving recycled phone numbers and new account sign ups, which fortunately only affected a very small number of our users. We are constantly evaluating and improving our protections and are committed to strengthening the security controls of our platform,” an Airbnb spokesperson told SecurityWeek.
The handling of the issue by Airbnb suggests that the company’s support staff is not well trained when it comes to handling reports describing security issues. While a majority of security-related issues are typically reported to vendors by professional bug bounty hunters, regular users identifying serious vulnerabilities is not unheard of, and these regular users are more likely to attempt to report their findings through a support channel rather than an official vulnerability disclosure program.
One example is the case of CVE-2019-6223, a FaceTime spying vulnerability uncovered last year by a 14-year-old. The teen found the flaw by accident and his attempts to report it to Apple were ignored before details of the issue were made public.
Related: Lawmakers Concerned About Apple’s Handling of FaceTime Spying Bug
Related: IBM Tells Researcher It Will Not Patch Serious Data Risk Manager Flaws













