A piece of ransomware designed to target OS X systems has been delivered to users via the official installer for the BitTorrent client Transmission.
The threat was discovered on March 4 by researchers at Palo Alto Networks. Experts noticed that two installers for Transmission 2.90 contained a new piece of OS X malware that they have dubbed KeRanger and which they believe is the first fully functional ransomware targeting OS X.
Since Transmission is an open source application, Palo Alto Networks believes the attackers created a malicious version that they planted on the official website after compromising it. The ransomware can bypass Apple’s Gatekeeper protection system because the malicious Transmission versions are signed with a valid app development certificate issued by Apple.
Once it infects a system, KeRanger looks for 300 different file types — including documents, images, multimedia files, archives, source code, emails, certificates and databases — and encrypts them using the AES specification.
Victims are asked to pay one Bitcoin (roughly $400) to get their files back. In order to prevent users from recovering their files from Time Machine backups, files associated with this application are also encrypted. The ransomware drops a text file containing instructions on how to buy Bitcoin and where to send it in return for the key needed to decrypt files held for ransom.
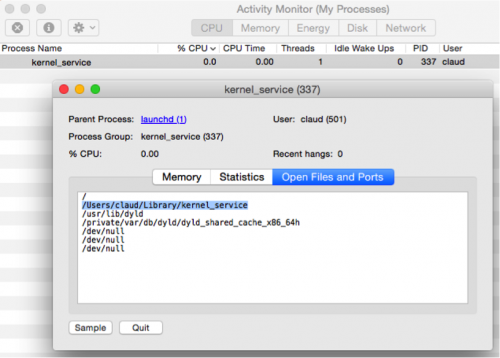
According to researchers, KeRanger was added to Transmission installers as a file named “General.rtf.” While this looks like a harmless document file, it’s actually a Mach-O executable that gets copied to ~/Library/kernel_service and executed before any user interface appears.
It’s worth noting that the threat doesn’t immediately start encrypting files on the infected system. Experts determined that KeRanger is designed to wait for three days before connecting to its command and control (C&C) server over the Tor anonymity network, and only then it begins the encryption process.
The developers of the Transmission BitTorrent client have released version 2.92, which removes the ransomware from users’ devices. Transmission 2.91 is not infected, but it doesn’t automatically remove KeRanger from systems, users have been told in a notice posted on the official website.
Apple has also taken steps to protect its customers. The company has revoked the certificate abused by KeRanger and it has updated the XProtect anti-malware feature to ensure that the threat cannot cause any damage on OS X systems.
Palo Alto believes the malicious version of the Transmission installers was served from the official website between March 4, 11a.m. PST, and March 5, 7p.m. PST. Experts have advised users to check their systems for file associated with the threat even if they downloaded the installer from other sources.
KeRanger is believed to be the first fully functional OS X ransomware. In June 2014, Kaspersky Lab reported finding such a threat, which the security firm dubbed “FileCoder,” but that malware seemed unfinished.
“As with most Mac malware this strain is exploiting the fact that users routinely login with privileged admin accounts and are free to download and install software from unknown sources. In this case the Gatekeeper check was bypassed using a genuine developer certificate, but as researcher Patrick Wardle has previously demonstrated there are plenty of ways an attacker can bypass Apple’s built-in security boundaries,” James Maude, senior security engineer at Avecto, told SecurityWeek.
“In the enterprise this problem is often magnified by the fact OS X users are logging on to devices with full admin accounts. KeRanger exploits the fact that the user has an admin account to install itself into the system library folder and infect the OS. On the Windows platform provisioning all your users with admin account is unthinkable, but when it comes to Macs organisations often ‘think different’,” Maude added.
“Macs in the enterprise are increasingly becoming the weak link in security that attackers are all too happy to exploit. We are seeing an increasing number of malware strains and attacks targeting Mac users who are often left almost unprotected. Our advice is to follow the same best practice on all your devices no matter what the operating system is: patching, least privilege and whitelisting applications,” the expert said.
Related: OceanLotus Trojan for OS X Evades Antivirus
Related: Mac OS X and iOS Infections and Threats on the Rise
















