A researcher has once again managed to bypass OS X’s Gatekeeper security feature, and the patch rolled out by Apple addresses the problem only temporarily.
Gatekeeper is designed to protect OS X users against malware downloaded from the Internet by automatically blocking applications that come from an unknown developer or ones that have been tampered with.
Patrick Wardle, director of research at Synack, has analyzed the inner workings of Gatekeeper for the past year.
The expert initially discovered a Gatekeeper bypass technique involving dynamic library (dylib) hijacking. He later found another method, which he disclosed at Black Hat USA and later, in more detail, at the Virus Bulletin conference in Prague.
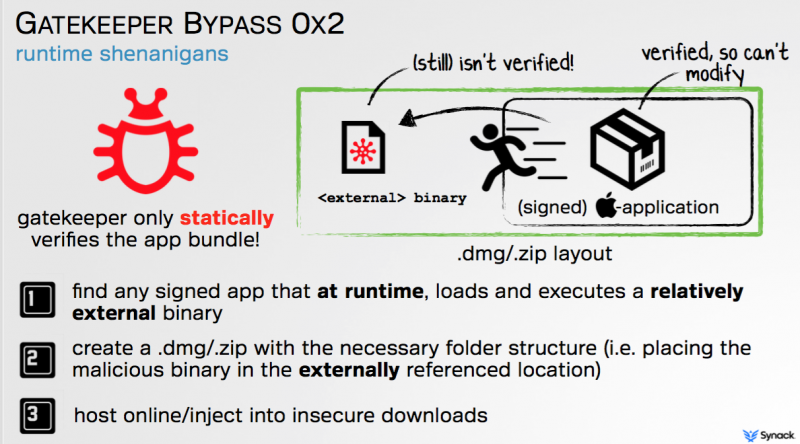
Wardle’s latest bypass method relies on the fact that Gatekeeper only statically checks app bundles, without verifying that they don’t execute a relatively external binary. This allows malicious actors to slip malware past the security system in a three-step attack.
The attacker must first find a signed application that loads and executes an external binary at runtime. The second step is to create a .dmg file in which the external binary is replaced with a malicious file. Finally, the attacker delivers the malicious .dmg file to users by injecting it into insecure download connections or by uploading it to third-party application stores.
Apple attempted to block Wardle’s attack method (CVE-2015-7024) with the release of OS X El Capitan 10.11.1.
However, the company’s fix was not very efficient since it focused on blacklisting the signed applications abused by Wardle in his demonstrations. In December, the expert simply identified another Apple-trusted binary and once again bypassed Gatekeeper.
The expert told SecurityWeek that Apple addressed this latest bypass by adding the abused binary to the OS X anti-malware system XProtect, specifically the XProtect.meta.plist file.
However, since the underlying issue has not been resolved, the Gatekeeper bypass could be revived at any time if another signed application that loads and executes an external library at runtime is found.
“I’m sure there are other binaries that could still be abused, as the systemic issue is still present,” Wardle said via email.
The researcher says Apple has not made any significant improvements to Gatekeeper over the past months, but the company is working on a more comprehensive fix for his bypass method.

