The enterprise security world is complex and confusing where we want to believe in the possibility of clean linear solutions for asymmetrical problems. Learning from past history and our current challenges should be enough of a lesson in the failure of security processes and products not delivering in their attempts to make the day-to-day routine of security professional lives easier. Each year we see more vendors with technology solutions and buzzwords that rarely live up to their hype and customers willing to believe or gamble for the chance at more visibility, lower business risk, or the chance to close a security gap.
Buzzword bingo
Let’s go through some historical examples.
“Big Data” has been a boon to cybersecurity from the aspect of providing the ability to aggregate and store voluminous and disparate data sets. Still, getting value from that stored data has been problematic. Storing data has become more trivial, but making sense of all that data still challenges us today.
“Security Orchestration” was supposed to be another savior of cybersecurity by automating away mundane tasks and supplementing security teams’ bandwidth to make the hard decisions easier. The reality is these solutions were too difficult to be implemented by most customers because their technical interfaces required more software engineering skills than security skills. This created more opportunities in the security services industry than in enterprise security, with MSPs being more than happy to provide python developers to their customers to make their expensive and unwieldy orchestration solution work.
“ML/AI” – don’t even get me started. While there are hopeful pockets of activity in the security industry here, a good majority of security vendors are more interested in applying AI/ML-themed marketing sheens on the product rather than actually putting useful working ML/AI in the product.
“Cloud Security” suffered from rampantly fast public cloud adoption by businesses and left enterprise security teams, and vendors for that matter, in the familiar position of playing from behind. Enterprise security teams scrambled to catch up with their business counterparts in securing the gaps created by cloud adoption. Initial cloud security vendors rushed to market trying to provide products to address these gaps, but many ended up with a narrow focus on product functionality or fell into the trap of trying to support multiple cloud service providers, which diluted the offering or made it unable to scale.
There are more examples, of course, but regardless of the security gap trying to be filled by a solution, the attention paid to helping the human behind the keyboard with better design and usability has always been overshadowed by more and better technological solutions with the focus on detection, integration, automation, and other security product ‘check boxes’ to increase their revenue. We are starting to see pockets of desire from the enterprise security community to solve the human problems in security rather than more technical solutions, but the definition of ‘solving for the human layer’ is still being defined and will need more time to gain momentum before vendors begin to address it.
Learning from outside cybersecurity
From a design and usability perspective, it’s important to understand what is happening outside of cybersecurity to learn valuable lessons which can be adapted for our purposes. If you look outside of the cybersecurity realm you’ll find many examples where design and usability are key to the success of the industry. In the financial sector, there are high-speed trading applications where being able to visually process information for quick decision-making is paramount. In the medical sector, there is telesurgery where a doctor can adeptly perform surgery from hundreds of miles away. And the consumer sector is full of products customers enjoy using.
And yet, the video game industry is most compelling when compared to cybersecurity. Game studios have spent many decades understanding their design principles and how it relates to their customer and usability. The most important of these principles equates to the gaming concept of ‘gameplay.’ Games with high-quality gameplay are engrossing and sometimes described as addictive. A simple definition of gameplay is the connection and tactical feel of how a player interacts with a game, separate and distinct from the graphics and sound effects. The quality of the gameplay is the measure of success or failure for the game. Hit the spot on gameplay and the gaming community will flock in droves to play your game.
Why is this important to enterprise security? If cybersecurity tools were less designed to look like Microsoft Office applications and more designed to enable the user would interest and engagement with the tool increase?
Another perspective to think about comes from academic researcher Lori Norton-Meier in a 2005 article where she said, “The video game has the potential to push an individual to learn and think cognitively, socially, and morally. Players actively create new virtual worlds; participate in complex decision-making; and think reflectively about choices that were made, including the design of the game.”
Let us remove video game references and insert cybersecurity terms and see how it reads:“Cybersecurity has the potential to push an individual to learn and think cognitively, socially, and morally. Security teams actively investigate networks; participate in complex decision-making; and think reflectively about choices that were made, including the design for the defense of their network.”
If someone told me the second quote, but not the first, I’d find the statement insightful. How much of this quote is relevant to:
• What we expect of our more experienced enterprise security professionals, and
• How we can better teach and upskill our less experienced enterprise security professionals?
Another perspective comes from a 2018 McAfee cybersecurity survey. Out of 300 managers and 650 security professionals, it was found that 92% believed skills fostered by video games – such as tenacity, logic, and predicting hostile strategies – could make the gaming community an ideal, untapped reservoir of candidates for the current staffing shortages in enterprise security.
There is also the irony of art imitating life where greater than 90% of cybersecurity professionals are frequent video game players, with greater than 65% having played a video game in the previous 24 hours.
The above are interesting data points and thoughts on some of the parallels between the video game & cybersecurity industries, but how do these help bring better usability and visual UX/UI design principles to security?
A real-time strategy gaming comparison
Let’s focus on one type of game genre, commonly referred to as real-time strategy games or RTS. The history of RTS games goes back 30 years, with famous examples being Warcraft, Command & Conquer, and Starcraft. The basic premise of RTS games is to do reconnaissance while building structures and units to main and acquire more resources to secure and defend areas the player controls in real-time.
The below graphic illustrates the expectations for success in winning an RTS video game while also showing the similarities between daily life in the enterprise security trenches.
Similarities
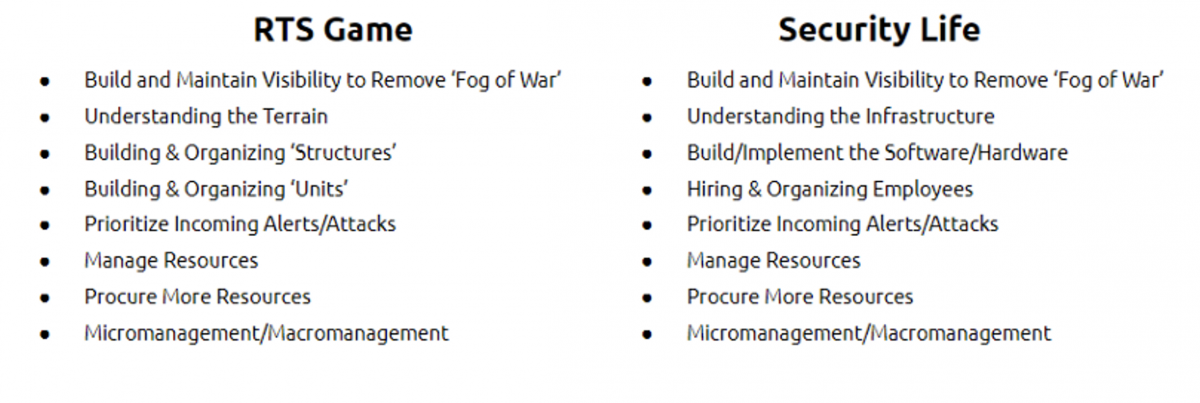
Conversely, looking at the differences is also enlightening.
Differences
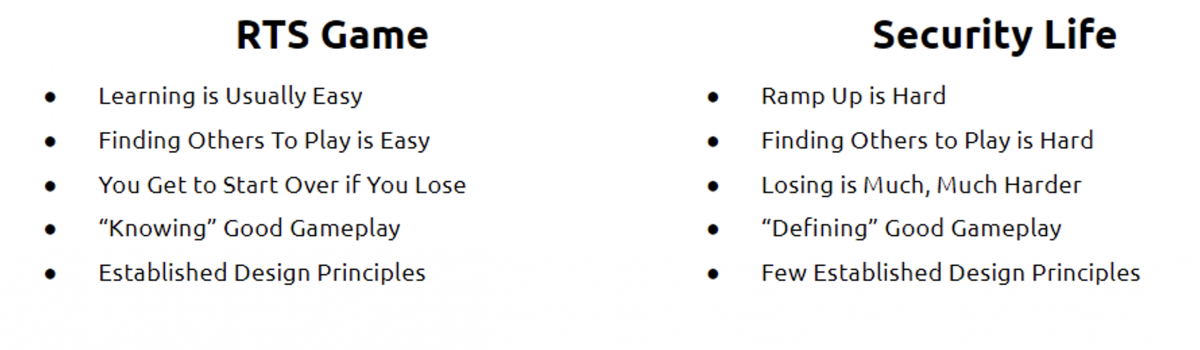 While the similarities are fascinating, it’s the differences that provide the most opportunity for cybersecurity. Over the years, RTS games’ usability has evolved to incorporate design principles that allow for information-dense user interfaces, which enable complex decision-making in a short amount of time in the demanding session they are played. While the graphics and interfaces all look aesthetically different, the underlying UX/UI design principles work very similarly. The design principle allows players to buy new versions of the same game or buy new RTS games from other vendors and have the advantage of a short learning curve to become highly proficient when picking up the new game. Essentially, RTS games have shared language, terminologies, and metaphors that reduce the bar for players to jump from game to game.
While the similarities are fascinating, it’s the differences that provide the most opportunity for cybersecurity. Over the years, RTS games’ usability has evolved to incorporate design principles that allow for information-dense user interfaces, which enable complex decision-making in a short amount of time in the demanding session they are played. While the graphics and interfaces all look aesthetically different, the underlying UX/UI design principles work very similarly. The design principle allows players to buy new versions of the same game or buy new RTS games from other vendors and have the advantage of a short learning curve to become highly proficient when picking up the new game. Essentially, RTS games have shared language, terminologies, and metaphors that reduce the bar for players to jump from game to game.
And that is where the above description and concept get interesting for cybersecurity as well. Does this mean gamification? No, that is a different topic for a different day. Nonetheless, taking into account all the similarities between what cybersecurity practitioners do daily and the idea of RTS games is ironic and compelling. It touches on how cybersecurity is a challenging problem, but video games are perhaps where we can go to learn from similar problem sets outside of cybersecurity and adopt and apply their success to cybersecurity.
In this article, I covered the persistent design and usability problem that cybersecurity has contended with. Security vendors have historically focused on buzzwords, technology sans usability, and marketing coats of paint rather than lending their attention to simplifying the daily grueling routines of security teams. I highlighted how the enterprise security industry can look to video games for some much-needed lessons in usability and design. The similarities between both industries make the case for the comparison, and the differences shed light on areas of opportunity for enterprise security.
Now that the context has been set in Part One, I will move on to takeaways in Part Two of ‘What Cybersecurity Can Learn From Video Games’. I will discuss the similarities between both industries in greater detail, highlighting why the comparison is salient. More importantly, I will discuss the differences between both industries, and how enterprise security can use lessons from video games to solve its own unique and pressing challenges. Until next time!












