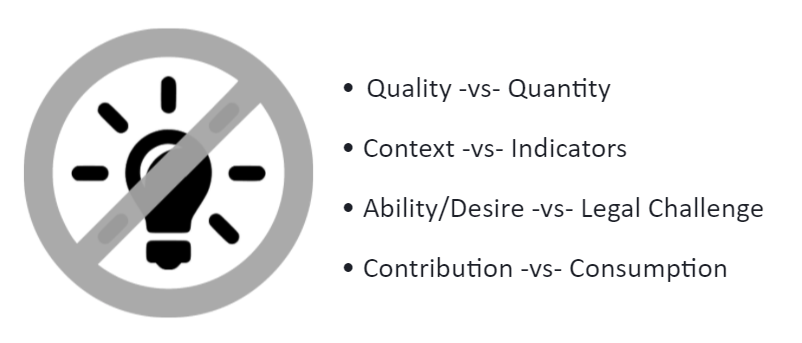
Enterprise security teams need to move from the consumption of crowdsourced threat intelligence (CTI) to an additional mode of contribution
Cybersecurity has an information sharing problem. We are a community with grand ideas around the concept of crowdsourced threat intelligence (CTI), but with little history or previous successes that show CTI as a viable idea. In this context, the crowdsourced data could be from the many open-source projects or the third-party vendors who provide threat intel. It is essentially the desire to aggregate valuable information sources and provide value back to those sources. The concept of crowdsourcing is not new to enterprise security teams – we have all been sharing our intel for a while, mostly in small private friendly circles through email, instant message, and other messaging platforms.