Researchers have discovered two vulnerabilities in Siemens’ SICAM Power Automation System (PAS). The vendor has patched one of the flaws and is currently working on addressing the other one.
SICAM PAS is an automation system used by energy companies worldwide to operate electrical substations. The Windows-based software product is advertised as scalable, flexible, easy to operate and cost-efficient.
Researchers at Positive Technologies analyzed the Siemens product and found that it’s plagued by two information disclosure vulnerabilities that can be exploited by a local attacker, ICS-CERT said in an advisory published on Thursday.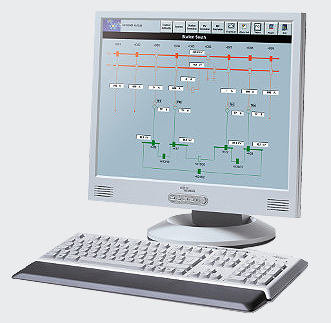
Experts discovered that user passwords are not protected properly, allowing an attacker to reconstruct the information (CVE-2016-5848). The second issue can be exploited by hackers to access sensitive configuration data (CVE-2016-5849).
“The attacker must have local access to the SICAM PAS system and certain database privileges or the database must be in a stopped state,” Siemens said in its own advisory.
Related: Learn More at the ICS Cyber Security Conference
Siemens addressed CVE-2016-5848 with the release of SICAM PAS 8.07 and is currently working on addressing CVE-2016-5849. Until a fix becomes available, the industrial giant has advised customers to contact its support center for instructions on how to mitigate the unpatched flaw.
Eaton ELCSoft Vulnerabilities
On Thursday, ICS-CERT also published an advisory describing vulnerabilities in a different product used in the energy sector. Researchers discovered that Eaton’s ELCSoft programming software, which is used by power grid operators to configure PLCs, is plagued by two memory corruption flaws that can be exploited to execute arbitrary code on the targeted system.
The issues, reported by Ariele Calgaviano through the Zero Day Initiative (ZDI), affect ELCSoft 2.4.01 and earlier, and they have been patched with a firmware update.
Related Reading: Siemens Patches Vulnerabilities in Industrial Automation Products
Related Reading: Vulnerabilities Found in Siemens SIPROTEC Protection Relays
















