VirusTotal on Friday provided clarifications on the recent data leak that resulted in the exposure of information on 5,600 of the threat analysis service’s customers.
News broke earlier this week that VirusTotal had exposed a file containing information on 5,600 registered customers, including names and email addresses.
Some of the records were associated with government organizations around the world, including the United States’ Justice Department, FBI, NSA and Cyber Command. The main concern was that the leaked information could be leveraged by threat actors in social engineering attacks aimed at impacted users.
In a blog post published on Friday, VirusTotal apologized to customers and shared some clarifications on the incident.
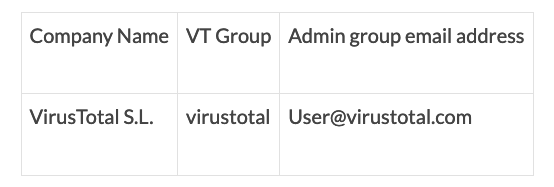
According to the Google-owned service, an employee accidentally uploaded a CVS file containing information on Premium account customers on June 29. The file contained information such as organization name, associated VirusTotal group name, and group administrator email addresses.
“First and foremost, we want to clarify unequivocally: This was not the result of a cyber-attack or a vulnerability with VirusTotal. This was a human error, and there were no bad actors involved,” explained Emiliano Martinez, head of product management at VirusTotal.
“Since this incident, we have implemented new internal processes and technical controls to improve the security and safeguarding of customer data,” Martinez added.
The VirusTotal representative clarified that the exposed list was only accessible to partners and corporate clients — only they have access to the Premium platform where the file was uploaded — and it couldn’t have been seen by malicious actors, nor by free account holders of anonymous users.
The file was removed within an hour. It was quickly noticed by VirusTotal customers who received alerts because they use Yara rules that search for files containing their own domains.
The company also noted that the employee who mistakenly uploaded the data to the platform was in possession of the information because it is critical to their role.
Related: API Flaw in QuickBlox Framework Exposed PII of Millions of Users
Related: Acronis Clarifies Hack Impact Following Data Leak
Related: Twitter Finds No Evidence of Vulnerability Exploitation in Recent Data Leaks

