[UPDATED] Enterprise software giant Atlassian has launched an investigation after a hacker group leaked information belonging to the company.
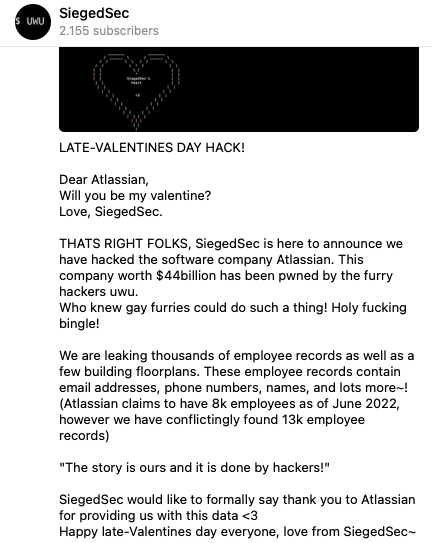
A threat actor named SiegedSec, whose members have claimed to be hacktivists, announced on its Telegram channel and hacking forums that it “hacked the software company Atlassian”.
They made 35 Mb of files public. This includes two image files apparently storing floor plans of Atlassian buildings in San Francisco and Sydney, and one file allegedly containing the information of 13,000 Atlassian employees, including names, email addresses, and phone numbers.
Atlassian is still investigating the incident, but it appears that the data stolen by the hackers is associated with workplace platform Envoy, which the software giant uses to coordinate in-office resources. Atlassian has pointed out that product and customer data was not at risk as it’s not accessible through the Envoy application.
Indeed, the leaked file that seems to contain Atlassian employee records does include numerous references to Envoy. However, the workplace company said it wasn’t actually hacked.
Envoy founder Larry Gadea said on Twitter that they are investigating the incident, but at the moment there is no evidence that the company’s systems have been breached. Instead, the attackers used an API key associated with Atlassian to access the data, “much like any other customer or user would do as part of regular service”.
SiegedSec has been around since February 2022, targeting dozens of organizations around the world. The hackers have defaced websites, hijacked online accounts, and leaked data allegedly stolen from victims.
It’s not uncommon for hacker groups like SiegedSec to make exaggerated claims about their attacks.
UPDATE: Envoy has provided SecurityWeek the following statement:
“Both Envoy and Atlassian security teams have been collaborating to identify the source of the data compromise. We found evidence in the logs of requests that confirms the hackers obtained valid user credentials from an Atlassian employee account and used that access to download the affected data from Envoy’s app. We can confirm Envoy’s systems were not compromised or breached and no other customer’s data was accessed.”
In addition, Atlassian explained that the credentials abused by the hackers were obtained from a public repository, where they had been mistakenly posted.
“The hacking group had access to data visible via the employee account which included the published office floor plans and public Envoy profiles of other Atlassian employees and contractors,” an Atlassian spokesperson said.
“The compromised employee’s account was promptly disabled early in the investigation which was proven effective in eliminating any further threat to Atlassian’s Envoy data,” they added.
Related: Atlassian Warns of Critical Jira Service Management Vulnerability
Related: CISA Warns of Attacks Exploiting Recent Atlassian Bitbucket Vulnerability
Related: Atlassian Expects Confluence App Exploitation After Hardcoded Password Leak

