A critical vulnerability in GitLab’s email verification process, which can lead to password hijacking, is being exploited in the wild, the US cybersecurity agency CISA warns.
Tracked as CVE-2023-7028 (CVSS score of 10/10), the flaw allows for password reset messages to be sent to email addresses that have not been verified, enabling attackers to hijack the password reset process and take over accounts.
GitLab patched the security defect in January 2024, warning that GitLab Community Edition (CE) and Enterprise Edition (EE) versions 16.1 to 16.7.1 are affected. Fixes were included in GitLab versions 16.5.6, 16.6.4, and 16.7.2 and backported to versions 16.1.6, 16.2.9, 16.3.7, and 16.4.5.
GitLab said at the time that it had not observed in-the-wild exploitation of CVE-2023-7028, but CISA on Wednesday added the bug to its Known Exploited Vulnerabilities (KEV) Catalog, saying it has evidence of active exploitation. SecurityWeek has not seen other reports of CVE-2023-7028 being targeted in attacks.
“GitLab Community and Enterprise Editions contain an improper access control vulnerability. This allows an attacker to trigger password reset emails to be sent to an unverified email address to ultimately facilitate an account takeover,” CISA notes.
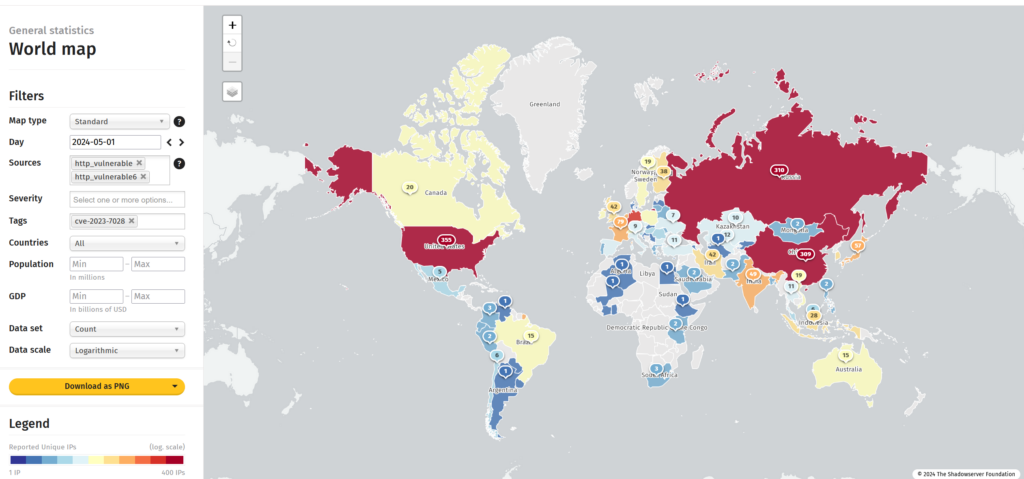
At the end of January, The Shadowserver Foundation warned that over 5,300 internet-accessible GitLab servers had not been patched against the vulnerability, but that number dropped to around 1,400 as of May 1, new data from Shadowserver shows.
As per Binding Operational Directive (BOD) 22-01, with CVE-2023-7028 added to CISA’s KEV list, federal agencies have until May 22 to identify vulnerable GitLab instances in their environments and apply the available patches.
While BOD 22-01 applies to federal agencies only, all organizations are advised to read GitLab’s advisory and apply the available patches and mitigations as soon as possible.
Related: Critical WordPress Automatic Plugin Vulnerability Exploited to Inject Backdoors
Related: Siemens Industrial Product Impacted by Exploited Palo Alto Firewall Vulnerability
Related: Over 1,400 CrushFTP Instances Vulnerable to Exploited Zero-Day














