Malware hunters in Google’s Threat Analysis Group (TAG) say government-backed hacking groups from different countries are feasting on a well-documented security flaw in the popular WinRAR file archiving utility more than three months after patches were released.
The WinRAR code execution vulnerability, tracked as CVE-2023-38831, was fixed in July after zero-day exploitation was detected but now, three months later, Google says APT groups linked to Russia and China are still using the exploit with success.
“Cybercrime groups began exploiting the vulnerability in early 2023, when the bug was still unknown to defenders. A patch is now available, but many users still seem to be vulnerable,” Google’s Kate Morgan said in a note documenting the APT discoveries. “After a vulnerability has been patched, malicious actors will continue to rely on n-days and use slow patching rates to their advantage.”
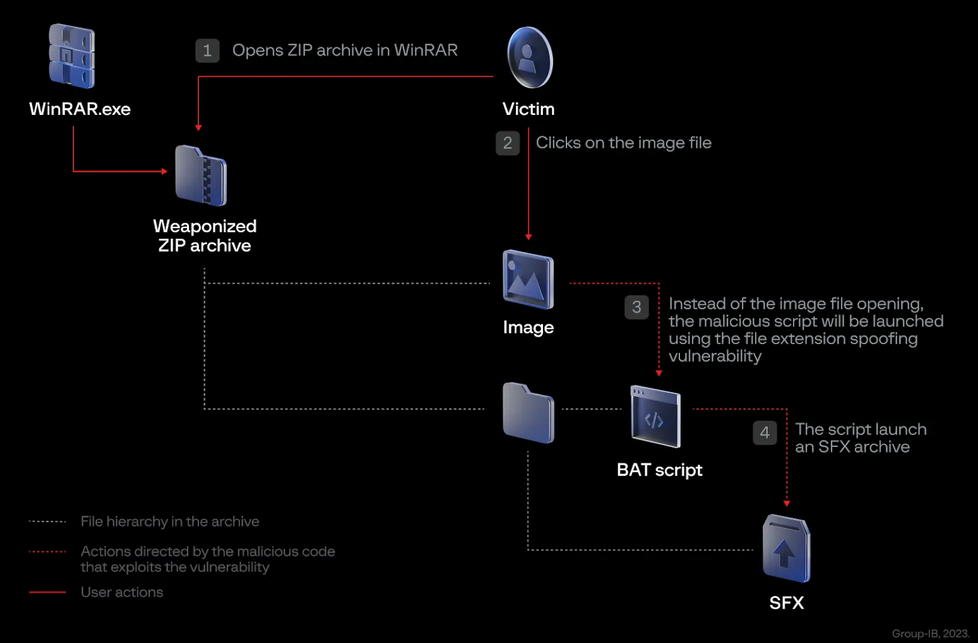
Morgan said the flaw, which allows attackers to execute arbitrary code when a user attempts to view a benign file (such as an ordinary PNG file) within a ZIP archive, has been known since at least April 2023 and immediately attracted the interest of threat actors.
“Hours after the blog post [about zero-day exploitation] was released, proof of concepts and exploit generators were uploaded to public GitHub repositories. Shortly after that, TAG began to observe testing activity from both financially motivated and APT actors experimenting with CVE-2023-38831,” Morgan added.
In one case, Google TAG detected the Russia-linked Sandworm delivering decoy PDF documents and malicious ZIP files exploiting the WinRAR bug. Sandworm, aligned with Russian Armed Forces’ Main Directorate of the General Staff (GRU) Unit, used the exploit to deliver a commodity infostealer that is able to collect and exfiltrate browser credentials and session information from infected machines.
Morgan documented another incident where APT28, another hacking team linked to Russian GRU, used a free hosting provider to serve CVE-2023-38831 to target users in Ukraine.
Google said it also caught government-backed groups linked to China launching WinRAR exploits in targeted attacks against users in Papua New Guinea.
“The widespread exploitation of the WinRAR bug highlights that exploits for known vulnerabilities can be highly effective, despite a patch being available. Even the most sophisticated attackers will only do what is necessary to accomplish their goals,” Morgan warned.
Software security defects in the WinRAR tool are constantly being targeted by cybercriminals and APT groups. SecurityWeek has reported on multiple WinRAR exploitation incidents recently, including usage by financially motivated hackers against traders and .gov-backed advanced threat actors.
Related: Traders Targeted by Cybercriminals in Attack Exploiting WinRAR Zero-Day
Related: WinRAR Vulnerability Exploited to Deliver New Malware
Related: Recently Patched WinRAR Flaw Exploited in APT Attacks
Related: Hackers Exploit WinRAR Vulnerability to Deliver Malware