Researchers have discovered a new Mac malware that encrypts files on compromised systems like a piece of ransomware, but also allows its operators to steal data and take full control of an infected device.
Initially named EvilQuest, the malware was later renamed ThiefQuest to avoid confusion as EvilQuest is the name of a video game. When the malware was first identified, none of the antivirus engines on VirusTotal detected the samples, but at the time of writing it is detected by over a dozen engines.
Malwarebytes has seen the malware being distributed as trojanized installers for popular macOS applications, including the Little Snitch firewall, the Mixed In Key and Ableton DJ apps, and a Google software update.
Patrick Wardle, a researcher who specializes in the security of Apple products, pointed out that since these installers are not signed, macOS alerts users before opening them, but people who download pirated software are likely to ignore the warning and install the malware on their device.
Wardle has published a detailed analysis of how ThiefQuest is installed, how it achieves persistence and its capabilities. Once the malware has been deployed, it starts encrypting certain types of files found on the system, including archives, images, audio and video files, documents, spreadsheets, presentations, databases and web files.
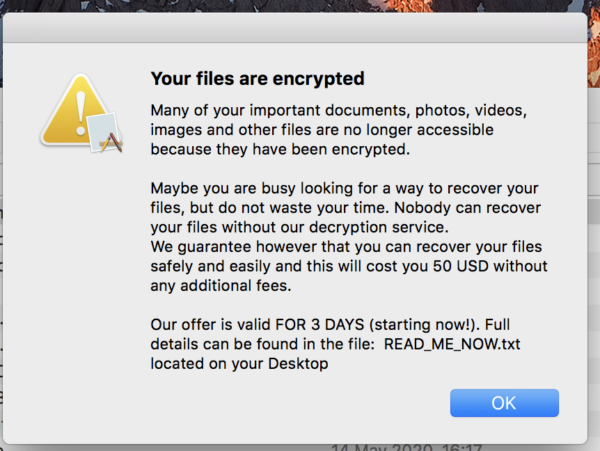
It then drops a text file informing users that their files have been encrypted and instructs them to pay $50 in bitcoin to recover them. A summary of the ransom note is also displayed in a modal window and its content is read out using the speech feature in macOS.
In addition to the ransomware capability, Wardle says, ThiefQuest can search for and exfiltrate files that could contain valuable information, such as cryptocurrency wallet data, and it can initiate a keylogger. The attacker can also remotely instruct the malware to execute commands and they can use it to create a reverse shell. Basically, an attacker could take full control of a device using these capabilities, Wardle warned.
Malwarebytes researchers say they have yet to determine if files encrypted by ThiefQuest can be recovered. However, an analysis conducted by Bleeping Computer suggests that ThiefQuest could actually be a wiper disguised as a ransomware as it may be impossible for users to recover their files even if they pay the ransom. The goal could be to use the ransomware tactics to hide the other malicious activities.
Bleeping Computer has pointed out that all victims are provided the same Bitcoin address for paying the ransom and the ransom note does not include an email address or other information for contacting the attacker. The attacker cannot tell who has paid the ransom and victims cannot get in touch with them to request the decryption tool once they pay up.
The ransom note claims that decryption will start automatically within two hours of the payment being processed, but that is unlikely to happen given how the malware has been designed. At the time of writing, the bitcoin address in the ransom note has not made any transactions.
Related: Mac Malware Delivered via Firefox Exploits Analyzed
Related: Repurposing Mac Malware Not Difficult, Researcher Shows
Related: Mac Malware Poses as Trading App













