A ransomware group has taken credit for the recent attack targeting aviation services company Swissport, and the cybercriminals claim to have stolen more than one terabyte of data.
Swissport discovered the breach on February 3 and disclosed the incident one day later. The company at the time could not share any information on the type of ransomware used in the attack or whether any data was stolen.
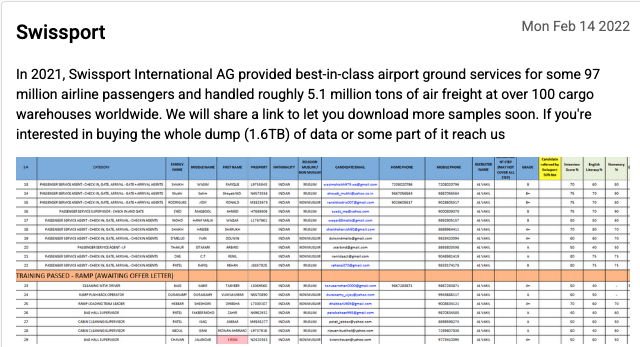
However, operators of a ransomware known as BlackCat, ALPHV and Noberus took credit for the attack on Monday, and published several files allegedly stolen from Swissport systems. Leaked files include passport copies, a database containing job candidate information, and an internal document.
Switzerland-based Swissport provides airport ground services and air cargo handling, with operations at 285 airports in 45 countries. It would not be surprising if the hackers’ claims that they managed to steal 1.6 TB of data are true.
The cybercriminals said on their Tor-based leak website (the site’s address was provided to SecurityWeek by digital risk protection firm Digital Shadows) that they are prepared to sell all of the stolen information or parts of it.
“While conducting our investigation, we learned that an unauthorized party posted data online that they claim to have stolen from Swissport,” Swissport told SecurityWeek. “We take these allegations seriously and are analyzing the files that were posted online as part of our ongoing investigation into the incident.”
“When we learned of the incident, we promptly took the affected systems offline, launched an investigation, notified law enforcement, and engaged leading cybersecurity experts to help assess the scope of the incident. At this point in time, we cannot provide any further information,” the company added.
The company said it’s in contact with customers, partners and employees regarding the incident.
The BlackCat ransomware emerged in mid-November 2021 and its developers have been trying to recruit affiliates. The ransomware has been used in attacks aimed at organizations in the United States, Europe and other regions. Victims include companies in the retail, construction, commercial services, transportation, insurance, professional services, pharma, telecoms, and other sectors.
Palo Alto Networks reported seeing ransom demands of up to $14 million, but the cybersecurity firm said BlackCat affiliates appear to be ready to negotiate.
Related: IT Services Firm Inetum Discloses Ransomware Attack

