Social media analytics service Social Blade has confirmed a security breach after a hacker offered to sell a database allegedly stolen from the company’s systems.
Social Blade monitors tens of millions of social media accounts, including on YouTube, Twitter, Twitch, Instagram, Facebook, and TikTok. The company helps content creators boost their channel’s popularity.
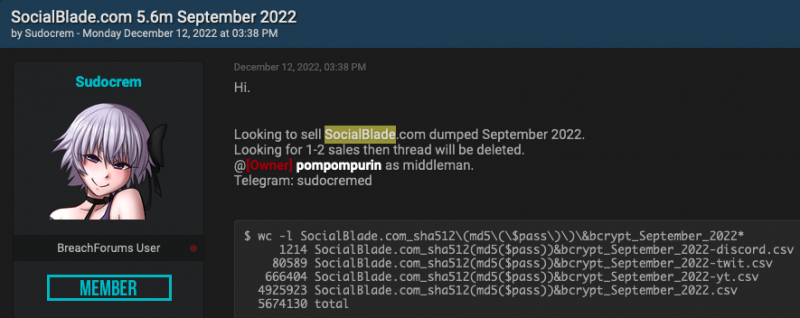
The Social Blade database was offered for sale on a hacker forum on Monday. The seller provided a sample of table names and content, claiming to have obtained 5.6 million records dated September 2022. The sample data suggests that many of the records contain user information.
The seller said the data will only be sold to one or two people. A known hacker has vouched for the authenticity of the database on the forum.
A few days after the database was put up for sale, Social Blade started privately informing customers about a data breach.
“On December 14th we were notified of a potential data breach whereby an individual had acquired exports of our user database and were attempting to sell it on a hacker forum,” Social Blade told users. “Samples were posted and we verified that they were indeed real. It appears this individual made use of a vulnerability on our website to gain access to our database.”
The company confirmed that email addresses, IP addresses, password hashes, client IDs and tokens for business API users, authentication tokens for connected accounts, and other non-personal and internal data was compromised. Roughly 0.1% of users also had their addresses leaked, but credit card information was not exposed, the company said.
Social Blade noted that the passwords are hashed using the BCrypt algorithm and it’s confident that they are not easy to crack so it’s not forcing a password reset, but users have been advised to change their password as a precaution.
The company says it has taken steps to prevent future incidents and advised customers to be on the lookout for phishing attempts that appear to originate from Social Blade.
This is not the first time hackers have obtained data from Social Blade’s systems. In 2016, the company confirmed getting hacked after someone leaked the details of nearly 300,000 website and forum users. At the time, the compromised password hashes were easy to crack and all user passwords were reset.

