New Research Shows 73% of IT Professionals Say Security is the Primary Reason for Deploying Mobile Device Management
InformationWeek Analytics today announced the release of a Mobile Device Management & Security study, which over 300 technology professionals shared insights on device management, mobile applications and security controls.
The results of the survey showed that security is the primary reason companies deploy, or plan to deploy mobile device management.
Key Findings in the Report: 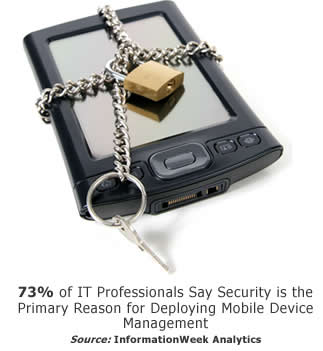
• 46% of respondents report smartphones will significantly increase in importance in relation to productivity.
• Four out of five business technology professionals say smartphones will become more predominant in their environments.
• Companies continue to roll out productivity applications, with more than a third pushing productivity apps out to mobile devices, compared to just 27% in our last survey.
• More than half of business technology professionals report having written policies and procedures for the treatment of mobile data, and an additional quarter have either policies or procedures; the remaining 25% don’t address the issue.
“Security will continue to drive the need for mobile device management tools,” says Lorna Garey, Content Director of InformationWeek Analytics. “Mobile devices provide increased productivity to companies and employees, however they present a clear risk to business technology executives and therefore is a top of mind issue.”
According to John Havener, CIO of IT consultancy BizTech of Arizona, “Mobile devices are changing the fastest of the technologies impacting the corporation, forcing IT leaders, in conjunction with corporate peers, to create an agile, responsive environment to empower users to benefit from those advancing capabilities. While it only consumes 20% of my day, it occupies 75% of my thought processes.”
The full report is available here












