LAS VEGAS – BLACK HAT USA 2022 – An analysis conducted by two researchers has revealed that some commercial cybersecurity products rely on algorithms that have been taken from other security tools without authorization.
The results of the research will be presented on Thursday at the Black Hat conference in Las Vegas by Tom McGuire, instructor at Johns Hopkins University, and Patrick Wardle, macOS security expert and founder of the Objective-See Foundation, a non-profit that provides free and open source macOS security resources.
The analysis focused on OverSight, a free tool offered via the Objective-See Foundation. The app enables users to monitor a Mac’s microphone and webcam, and alerts them whenever the mic is activated or the camera is accessed by a process.
The analysis led to the discovery of three security tools — developed by three different companies — that used OverSight algorithms without authorization. OverSight has been available as a free tool since 2016, but it was only made open source in 2021. Reverse engineering it in an effort to create commercial products would be unethical, if not illegal.
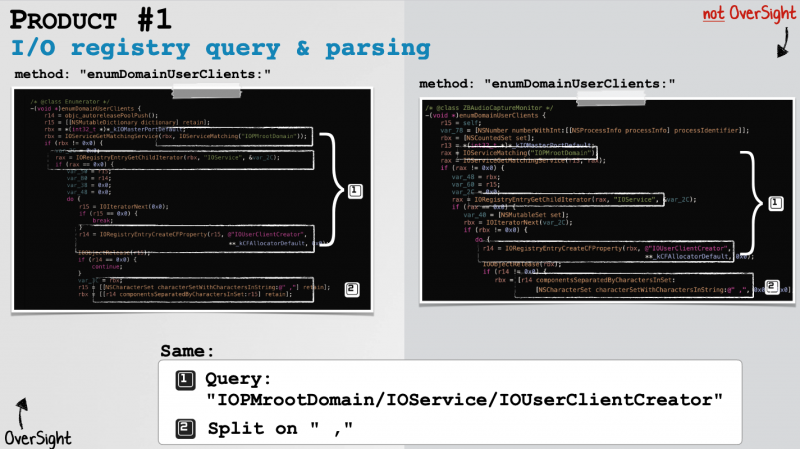
Using Google and Yara rules, the researchers identified commercial products using the same method names, paths, strings, undocumented registry keys, and parsing logic as OverSight.
The offending companies were contacted and provided with proof that OverSight algorithms had been used in their products without authorization. They acknowledged the issue — even though one of the firms only took the researchers seriously after being faced with the possibility of public backlash — and promised to remove the code, and even offered financial compensation.
Wardle told SecurityWeek that the compensation offered by the companies was reasonable — even if it was only a ‘drop in the bucket’ for them. The money will be used by the Objective-See Foundation for its Objective by the Sea conference, books and free tools.
However, Wardle said, the most important aspect is that all of the companies seemed eager to make changes and ensure that such practices are avoided in the future, which was one of the project’s main goals, along with bringing attention to the issue.
The companies that used the algorithms without authorization have not been named, but Wardle told SecurityWeek that they were both small and larger companies that had been using the stolen intellectual property for various products, including simple utilities and bigger macOS security products. A majority were dedicated cybersecurity companies, but the algorithms were also misused by a tech company.
On the other hand, it’s worth mentioning that the researchers concluded that in a majority of cases the infringement is the work of a single — possibly naive — developer, rather than ‘malice of the entire corporation’.
“I went in thinking the entire corp. was likely conspiring to steal from my non-profit, whereas that really wasn’t the case,” Wardle said.
The goal of this research was to encourage others to look into these practices and help developers find out if their code has been stolen — the researchers believe this practice is likely more common than we think. However, Wardle noted that you need both a software developer and a competent reverse engineer to identify this type of theft.
“It doesn’t matter if your code is closed-source — if people want to steal it they will,” Wardle said. “I knew that technically this wasn’t complicated, but figured the fact that it wasn’t open-source (originally) would be a clear ‘hey, this is private, don’t steal’. Apparently not.”
Related: Repurposing Mac Malware Not Difficult, Researcher Shows
Related: Hackers Can Bypass macOS Security Features With Synthetic Clicks