Hackers can use synthetic clicks to bypass many of the privacy and security features implemented last year by Apple in its macOS operating system, a researcher has revealed.
Patrick Wardle, co-founder and chief research officer at Digita Security, a company that specializes in security products and services for macOS, has discovered a vulnerability that allows hackers, malware or unauthorized applications to locally bypass some features announced by Apple at its 2018 Worldwide Developers Conference (WWDC).
At the time, Apple revealed that macOS Mojave would alert users every time an application wants to access their camera, microphone, events, contacts, location, photos, backups, Safari data, history, and mail database, or when an app attempts to obtain admin privileges or remotely control processes.
Over the weekend, just as Apple was preparing to kick off the 2019 WWDC, Wardle revealed at his company’s Mac security conference, Objective by the Sea, that a “subtle code-signing issue” in macOS allows any trusted application to be subverted to generate synthetic clicks, which should normally be prevented by the operating system.
Malicious actors can bypass the alerts presented to macOS users when an application wants to access their data or device through a synthetic click on the “OK” button in privacy and security prompts.
Wardle says that while such an attack could raise suspicion from the user given that they might see the action taking place on their screen, an attacker could trigger the exploit when the screen is dimmed (when the display is going to sleep).
It’s worth noting that this is a second stage attack. The attacker needs to have access to the targeted Mac before executing the exploit, but Wardle told SecurityWeek that no special privileges are required to perform an attack.
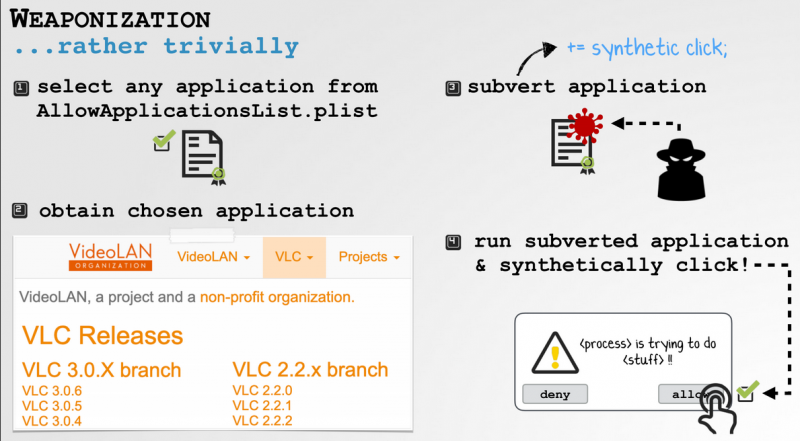
The attack involves the Transparency Consent and Control (TCC) system, which maintains databases for privacy control settings, including what component each application is allowed to access. The system also includes a compatibility database, stored in a file named AllowApplicationsList.plist, which serves as a whitelist with rules for granting access to protected functions for specific versions of apps with specific signatures.
An attacker can pick an application from this whitelist, make malicious modifications to it, and then execute it to generate synthetic clicks. The modifications to the targeted app are not detected by Apple due to a subtle flaw in the code validation checks.
Wardle explained that the attacker can simply download a modified version of the targeted app and run it.
“Basically, the system will always allow synthetic clicks from the whitelisted apps (on the whitelist) — it doesn’t care if the app was installed by the user, or if malware downloaded and ran it, specifically to generate clicks,” the researcher said via email.
For instance, an attacker can target the popular VLC media player and simply add a malicious plugin to the application in order to be able to generate synthetic clicks.
Wardle has identified several vulnerabilities in macOS that allow synthetic clicks, including one disclosed last year at DefCon. Apple has been patching the weaknesses, but Wardle says the patches are often incomplete and he believes “Apple has struggled to prevent synthetic click attacks.”
Wardle told SecurityWeek that he reported his findings to Apple roughly one week ago and the company confirmed receiving his report. However, it’s unclear what action the company plans on taking.
In the meantime, the expert has pointed out that GamePlan, an endpoint protection product designed by Digita Security for enterprise Mac fleets, can detect these types of synthetic clicks.
SecurityWeek has reached out to Apple for comment and will update this article if the company responds.
Related: macOS Mojave Patches Vulnerabilities, But New Flaws Already Emerge
Related: New Tool Detects Evil Maid Attacks on Mac Laptops
Related: How Antivirus Software Can be the Perfect Spying Tool

