A team of researchers has developed malware designed to target modern programmable logic controllers (PLCs) in an effort to demonstrate that remote Stuxnet-style attacks can be launched against such industrial control systems (ICS).
The researchers are from the Georgia Institute of Technology and they have published a paper detailing this ICS security project.
In the case of traditional PLCs, an attacker can target the control logic layer or the firmware layer. Firmware attacks can provide a high level of device control and are difficult to detect, but the malware can be challenging to deploy. Control logic malware is easier to deploy, but also easier to detect. Both of these scenarios require the attacker to have privileged access to the targeted organization’s industrial network.
In the case of modern PLCs, many include a web server and they can be remotely configured, controlled and monitored through dedicated APIs and a regular web browser that serves as a human-machine interface (HMI).
While these modern PLCs can provide many benefits for organizations, the Georgia Tech researchers caution that they can also significantly expand the attack surface of ICS.
To demonstrate the risks, the researchers developed what they call web-based PLC malware, which resides in the controller’s memory, but is executed client-side by the browser-equipped devices present in the ICS environment. The malware can abuse the PLC’s legitimate web APIs to cause disruption to industrial processes or cause damage to machinery.
This new PLC malware can be easy to deploy and difficult to detect. Initial infection can be done through physical or network access to the targeted web-based HMI, but the malware can also be deployed directly through the internet by hijacking the HMI using cross-origin vulnerabilities.
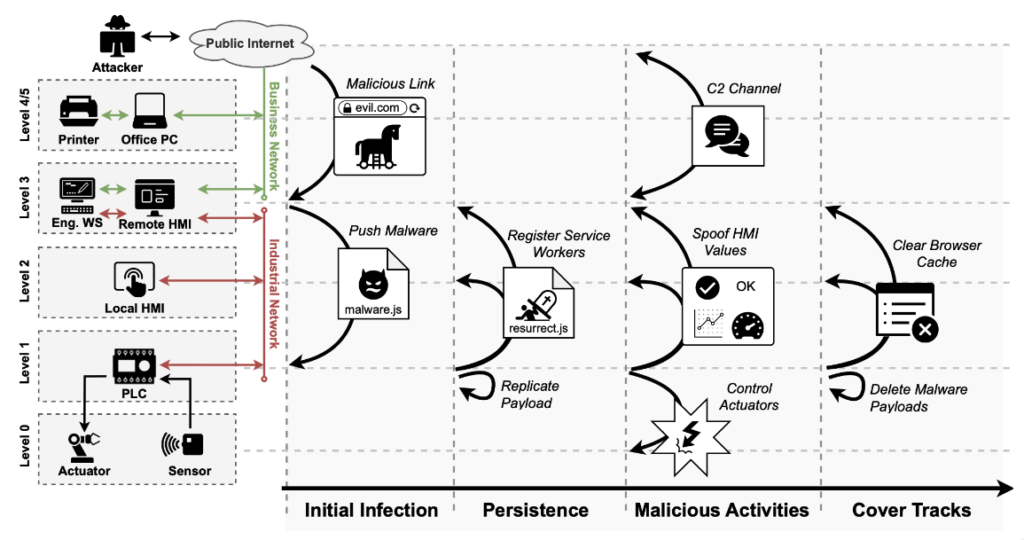
For persistence, this new type of PLC malware leverages service workers, which allow JavaScript code to burrow into the browser cache and execute independently of the web page that installed it. In addition, they will continue running for up to 24 hours after the file has been removed from the server. Using this method, the malware can survive firmware updates, new web-based HMIs, and even hardware replacements.
Once it has been deployed, the malware’s capabilities depend on the power of the legitimate web-based APIs that are used, and some of these APIs are very powerful. For instance, they can be leveraged to directly overwrite input/output values, abuse HMI inputs, change set points and safety settings, spoof the HMI display, update administrator settings, and even for real-time data exfiltration.
The researchers said the malware can also have a command and control (C&C) connection, even if the targeted PLC is in an isolated network.
Once the threat actor carries out the desired tasks, it can cover its tracks by getting the malware to destroy itself, overwrite the malicious payload with a benign payload, unregister all service workers, and potentially even conduct a factory reset of the device.
Read: Dutch Engineer Used Water Pump to Get Billion-Dollar Stuxnet Malware
The researchers demonstrated their work by developing a piece of malware named IronSpider, which they designed to target Wago PLCs. The simulated attack involved exploitation of previously unknown vulnerabilities to deploy the malware when the targeted operator looks at a specially crafted ad banner. The malware can sabotage an industrial motor to cause damage while spoofing the HMI screen to display normal values and avoid raising suspicion.
Some of the Wago PLC vulnerabilities were described last year by SecurityWeek following a chat with Ryan Pickren, one of the Georgia Tech researchers involved in this PLC malware project.
IronSpider has been compared to the notorious Stuxnet malware, which targeted Iran’s nuclear program more than a decade ago.
“Stuxnet sabotaged Iranian nuclear facilities by modifying the analog output signal to variable-frequency drives that controlled uranium enrichment centrifuges. A direct result from this sabotage was the physical destruction of over 1,000 centrifuges and a 30% reduction in operational capacity at the facilities,” the researchers said in their paper.
They added, “Our prototype malware, IronSpider, was able to achieve a fundamentally similar attack using a drastically different approach. Stuxnet attacked PLCs via control logic malware that it deployed via compromised engineering workstations […]. IronSpider, however, used web-based malware that it deployed using a malicious website without needing to compromise any peripheral systems.”
While the attack was demonstrated against a Wago product, the researchers determined that this type of PLC malware can also be used against Siemens, Emerson, Schneider Electric, Mitsubishi Electric, and Allen Bradley PLCs as well. The attacks against these controllers involve exploitation of newly discovered or previously known vulnerabilities. In some cases, FTP passwords, insecure protocols or insiders are required for an attack.
The experts have created a vendor-agnostic framework that can be used to build and analyze web-based PLC malware.
“This framework explores each stage using widely applicable strategies that can be used against most modern PLC models and presents an overview of how malicious front-end code can subvert the integrity of ICS environments by methodically compromising PLCs’ web properties. This framework can be used as a benchmark in future studies across any PLC vendor and model,” the researchers explained.
Related: CISA Warns of Unitronics PLC Exploitation Following Water Utility Hack
Related: Omron PLC Vulnerability Exploited by Sophisticated ICS Malware
Related: CosmicEnergy ICS Malware Poses No Immediate Threat, but Should Not Be Ignored
















