Earlier this month, security researchers from FireEye discovered a new IE 10 Zero-Day exploit (CVE-2014-0322) that was being used in a watering hole attack on the US Veterans of Foreign Wars’ website.
Dubbed “Operation SnowMan” by FireEye, the attack targets certain versions of Internet Explorer with Adobe Flash and originally was used in more targeted attacks against a limited audience.
Now, according to Symantec, the attacks are much more widespread and no longer being used in only targeted attacks.
“We’ve observed trends suggesting that attacks targeting this vulnerability are no longer confined to advanced persistent threats (APT) — the zero-day attacks are expanding to attack average Internet users as well,” Symantec wrote in a blog post Tuesday.
“This is not a surprising result, as the vulnerability’s exploit code received a lot of exposure, allowing anyone to acquire the code and re-use it for their own purposes.”
Symantec witnessed a large uptick in attempted zero-day attacks in many parts of the world on Feb. 22, including both targeted and drive-by download attacks. Users visiting Japanese sites have particularly been targeted after multiple sites were compromised to host the drive-by download, Symantec said.
Researchers at Websense said the vulnerability was being used as early as Jan. 20, including an attack that targeted organizations associated with the French aerospace association GIFAS.
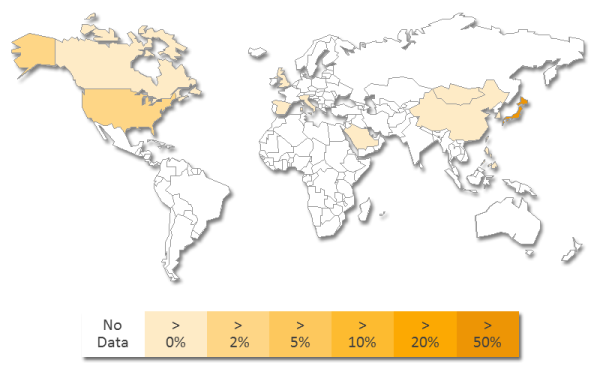
Attacks targeting CVE-2014-0322 around the world (Credit: Symantec)
Based on the file components used in the attacks, Symantec believes the same attacker(s) are behind the majority of the attacks.
If the attack is successful, the exploit drops a banking Trojan (Infostealer.Bankeiya) that captures login details from certain banks.
Microsoft has not yet issued a patch to fix the vulnerability, but did issue a fix-it tool on Feb. 20 to help users address the issue.
According to Microsoft, the vulnerability exists in the way IE accesses an object in memory that has either been deleted or not properly allocated. The vulnerability can corrupt memory in a way that allows an attacker to execute arbitrary code, Microsoft explained in an advisory.














