LockBit ransomware threat actors have taken credit for the recent attack on cybersecurity firm Entrust and they are threatening to leak the stolen files.
Dominic Alvieri, the researcher who broke the news about Entrust suffering a data breach, noticed on Thursday that Entrust has been added to the LockBit 3.0 Tor-based website.
The black hat hackers are threatening to leak all the stolen data on August 19, at 20:33 UTC, exactly 24 hours after they announced hacking Entrust.
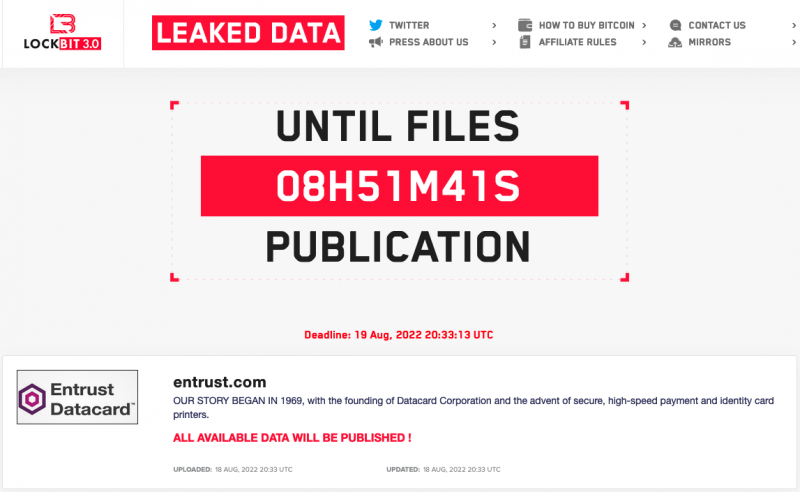
When the Entrust breach came to light in July, some researchers revealed that a known ransomware group was behind the attack, but no ransomware was named.
In its statement at the time, Entrust confirmed that threat actors had gained access to systems used for HR, finance and marketing, but said there was no evidence that the operation or security of its products and services was impacted.
SecurityWeek has reached out to Entrust for comment and will update this article if the company responds.
Entrust is a Minneapolis-based company that provides security solutions for user and machine identities, payments, and digital infrastructure. The firm’s services are used across 150 countries, including by some of the world’s largest organizations.
LockBit operators on Thursday also announced stealing files from US engineering giant Wabtec after breaching the company’s systems. News of a ransomware incident at Wabtec first emerged in late June.
SecurityWeek has reached out to Wabtec for comment.
Related: Car Parts Giant Denso Targeted by Ransomware Group
Related: Ransomware Gang Leaks Files Stolen From Industrial Giant Parker Hannifin
Related: Ransomware Gang Threatens to Leak Files Stolen From Tire Giant Bridgestone















