A well-known ransomware group is threatening to leak files stolen from tire and rubber giant Bridgestone Americas.
The cyberattack came to light in late February. Bridgestone at the time decided to disconnect many of its manufacturing and retreading facilities in the Americas from its network, which led to some plant operations getting shut down and employees being sent home. The company has 50 production facilities and 55,000 employees.
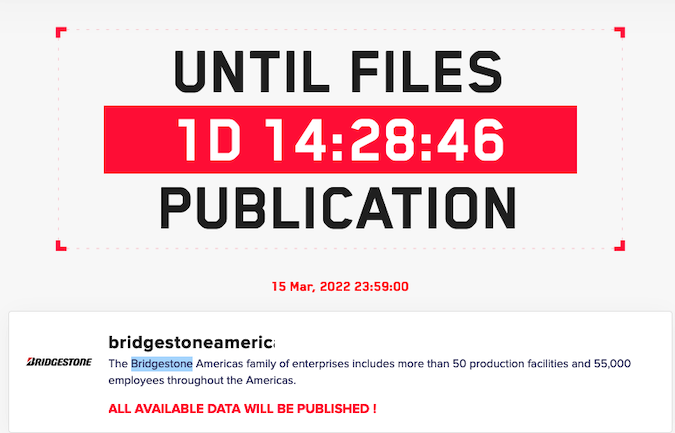
A cybercrime gang that has been using the LockBit 2.0 ransomware has taken credit for the attack on Bridgestone and is now threatening to make public “all available data.” At the time of writing, the timer on the group’s website shows that the company has less than two days to pay a ransom and avoid a data leak.
Nashville, Tennessee-based Bridgestone discovered the breach on February 27. It has now confirmed that ransomware was involved and that data from “a limited number” of systems has been stolen.
Law enforcement has been notified and Accenture Security has been called in to assist with the investigation.
It’s unclear how much money the hackers are hoping to make, but they are known to demand tens of millions of dollars from big companies.
The LockBit 2.0 gang has taken credit for several high-profile attacks over the past months, including one that targeted Accenture. The cybercriminals published thousands of files allegedly stolen from the consulting giant.
The group recently also claimed to have breached systems belonging to France’s Ministry of Justice. The files allegedly belonging to the Ministry of Justice have also been made public.
In an alert issued in February, the FBI warned organizations about LockBit 2.0 attacks. The agency has provided indicators of compromise (IoC) and other technical details to help companies detect and prevent attacks.
Related: Ransomware Operators Leak Data Stolen From Wind Turbine Giant Vestas
Related: University Project Cataloged 1,100 Ransomware Attacks on Critical Infrastructure
Related: Swissport Investigating Ransomware Group’s Data Leak Claims















