A notorious cybercrime group has leaked several gigabytes of files allegedly stolen from US industrial components giant Parker Hannifin.
Parker Hannifin specializes in motion and control technologies, and it provides precision engineered solutions for organizations in the aerospace, mobile, and industrial sectors.
In a Tuesday regulatory filing, the Fortune 250 company said it detected a breach of its systems on March 14.
Upon discovering the intrusion, Parker shut down some systems and launched an investigation. Law enforcement has been notified and cybersecurity and legal experts have been called in to assist.
The investigation is ongoing, but the company has confirmed that some data was accessed and taken, including personal information of employees.
“Based on its preliminary assessment and on the information currently known, the incident has not had a significant financial or operational impact and the Company does not believe the incident will have a material impact on its business, operations or financial results,” Parker stated. “The Company’s business systems are fully operational, and the Company maintains insurance, subject to certain deductibles and policy limitations typical for its size and industry.”
While the company has not shared any additional information regarding the incident, SecurityWeek has checked the websites of major ransomware groups and found that the notorious Conti gang has taken credit for the attack on Parker.
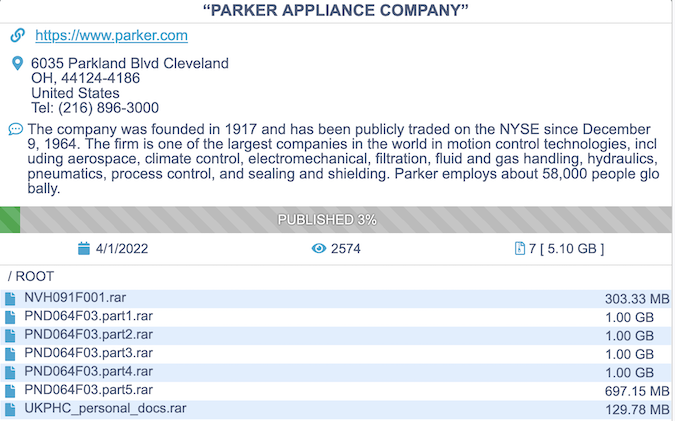
The hacker group has published more than 5 Gb of archive files apparently containing documents stolen from Parker, and that may be only a small fraction of the total data they have obtained — the Conti website indicates that only 3% of the stolen data has been leaked.
The hackers typically tell victims that they have to pay millions of dollars to recover encrypted files and prevent stolen data from getting leaked.
The cybercriminals have targeted hundreds of organizations over the past years, but the group itself became a target in February, after it expressed support for the Russian government following its invasion of Ukraine.
An individual claiming to be a Ukrainian cybersecurity researcher has leaked vast amounts of Conti data, including malware source code, chat logs, credentials, email addresses, and C&C server details.
The leaked information showed that Conti operates just like a regular company, with contractors, employees and HR problems. An analysis conducted by incident response firm BreachQuest revealed that Conti spent roughly $6 million on employee salaries, tooling and professional services in the past year alone.
Related: U.S. Warns of Conti Ransomware Attacks as Gang Deals With Leak Fallout
Related: Ransomware Gang Threatens to Leak Files Stolen From Tire Giant Bridgestone
Related: Financially Motivated Hackers Use Leaked Conti Ransomware Techniques in Attacks















