A notorious ransomware group is offering to sell files allegedly stolen from German car parts giant Continental for $50 million.
Continental reported in August that it had been targeted in a cyberattack that resulted in hackers accessing some of its systems. The company said at the time that the attack had been “averted” and that business activities were not affected.
The LockBit ransomware group recently revealed on its leak website that it was behind the attack on Continental and threatened to make public information stolen from the company.
Shortly after announcing the Continental hack, the cybercriminals published what appeared to be messages exchanged between them and the company’s representatives. The messages suggested that negotiations had failed.
The hackers have now published four screenshots to demonstrate that they do possess data from Continental systems. There is also a timer that suggests more data will be leaked on November 10.
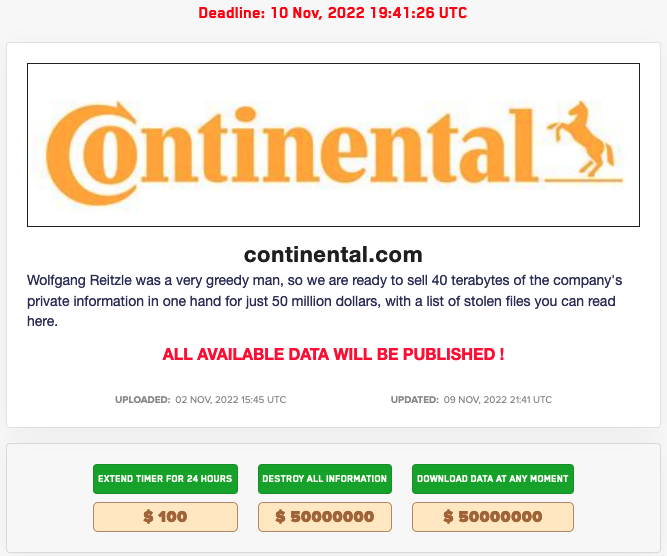
In addition, the page dedicated to the automotive company now displays three buttons. One of them can be used to extend with 24 hours the time until files are published, which costs $100. Two other buttons can be used to ‘destroy all information’ or ‘download data at any moment’ — both of these options have a $50 million price tag.
The option for destroying the information is likely meant for Continental. Given the ransom amount, the attackers likely believe the stolen information can be of great value to the victim’s competitors.
The hackers claim to have stolen a total of 40 Gb of files and the screenshots they have published suggest that they have gained access to technical documents and source code.
“[Continental board chairman] Wolfgang Reitzle was a very greedy man, so we are ready to sell 40 terabytes of the company’s private information in one hand for just 50 million dollars, with a list of stolen files you can read here,” the cybercriminals wrote on their website.
Continental has yet to respond to any of SecurityWeek’s requests for additional information.
However, the company did confirm to the Handelsblatt German-language business newspaper that the hackers did manage to steal data from its systems. Continental said its investigation is ongoing.
LockBit has been around since 2019 and the LockBit 2.0 ransomware-as-a-service operation emerged in June 2021. It has been one of the most active ransomware operations, accounting for nearly half of all ransomware attacks in the first half of 2022. When LockBit 3.0 was announced in June 2022, the cybercriminals also launched a bug bounty program offering up to $1 million for vulnerabilities and information on competitors.
Related: LockBit Ransomware Site Hit by DDoS Attack as Hackers Start Leaking Entrust Data
Related: LockBit Ransomware Abuses Windows Defender for Payload Loading















