The notorious LockBit ransomware group is threatening to publish files allegedly stolen from German car parts giant Continental.
On its Tor-based leak website, the group says all files — the exact quantity of data or its type is not being specified — will be published on November 4, three hours after the publication of this article.
Continental did say in August that it had been targeted in a cyberattack, with hackers infiltrating some of its IT systems.
“The company detected the attack in early August and then averted it. Continental’s business activities have not been affected at any point. The technology company maintains full control over its IT systems,” Continental said at the time.
The company has not shared any additional information about the attack, but it did suggest at the time that some data may have been stolen.
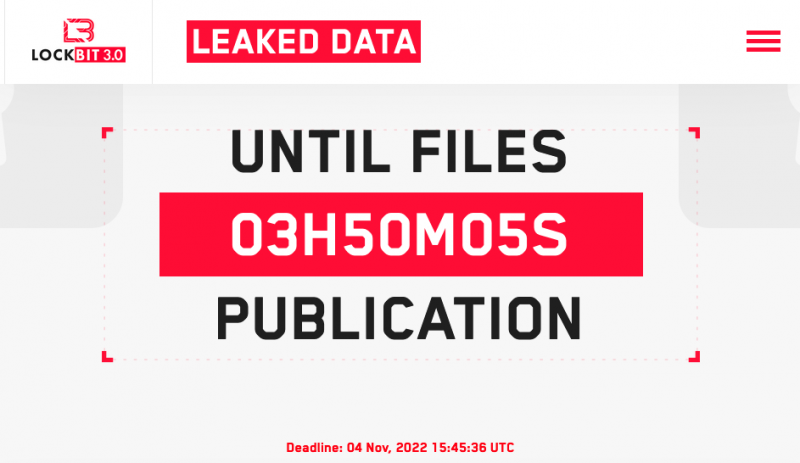
In addition to files, the LockBit ransomware group appears to be threatening to make public the chat logs of conversations between the cybercriminals and the automotive giant. If the attack disclosed by Continental in August was conducted by LockBit, it’s possible that the company has been trying to negotiate with the hackers until now.
SecurityWeek has reached out to Continental for clarifications and will update this article if additional information is provided by the company.
“Over the last year we have seen a dramatic rise in the number of attacks caused by the LockBit ransomware group, with Continental the latest victim to have their data threatened to be published,” said Raj Samani, SVP chief scientist at Rapid7. “Our research shows that LockBit’s market share in ransomware attacks per group has increased from 1% in 2020 to 4% in 2021, and this will only grow if they are allowed to continue stealing sensitive data and selling it on for profit.”
Darren Williams, CEO of ransomware specialist Blackfog, commented, “Companies within the automotive sector are typically large, complex organizations with valuable assets under management, so it comes as no surprise that ransomware groups are targeting them. What is surprising is that multinational organizations are still relying on technologies that are not up to the job of preventing ransomware.”
Williams added, “The recent attack on UK auto dealer Pendragon, which had a record breaking ransom demand of £54 million, clearly demonstrates how lucrative this sector could be for cybercriminals. Worryingly, the trend for targeting this industry will continue unless investment is made in newer technology designed to prevent modern threats.”
Related: LockBit Ransomware Site Hit by DDoS Attack as Hackers Start Leaking Entrust Data
Related: LockBit 3.0 Ransomware Emerges With Bug Bounty Program
Related: LockBit Ransomware Abuses Windows Defender for Payload Loading















