Publicly available hacking tools, many of which have been developed for research and testing purposes, lower the bar for threat actors looking to target industrial control systems (ICS) and operational technology (OT) networks, FireEye warned this week.
The cybersecurity firm told SecurityWeek that its Mandiant Intelligence team tracks nearly 100 tools that can be used to exploit vulnerabilities in ICS or interact with industrial equipment in an effort to support intrusions or attacks. The company also tracks hundreds of exploit modules developed for frameworks such as Metasploit, Core Impact and Immunity Canvas.
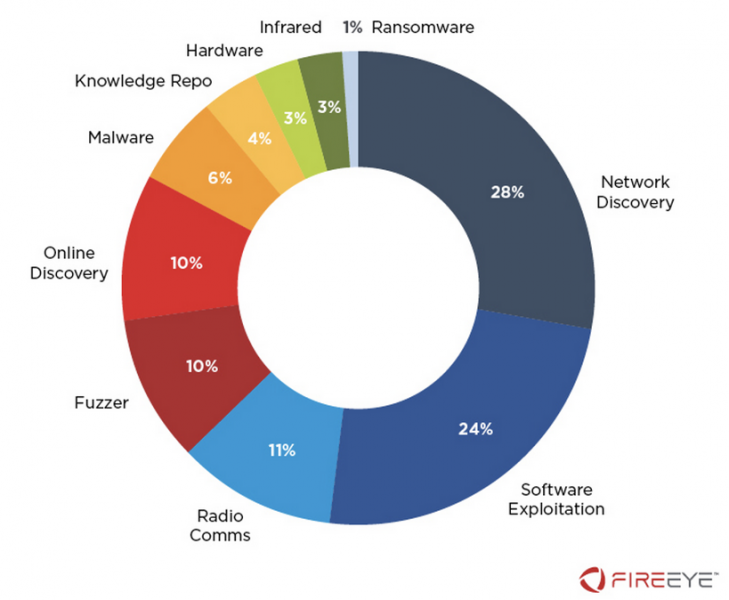
Of the ICS hacking tools tracked by FireEye — the company calls them ICS cyber operation tools — 28% are designed for discovering ICS devices on a network and 24% for software exploitation. Other tools are related to low-power radios, fuzzers, ICS devices connected to the internet, malware, hardware interaction, infrared ports, knowledge repositories, and ransomware.
FireEye says a majority of the tools are either vendor agnostic or designed to target the products of major manufacturers such as Siemens, Schneider Electric, ABB, GE, Rockwell Automation, and Wind River Systems.
In the case of modules designed for exploitation frameworks, FireEye has been tracking hundreds of ICS-specific modules covering a total of more than 500 vulnerabilities. Worryingly, 71 percent of these vulnerabilities are described by the company as “potential zero-days.”
“When we say potential zero day vulnerability, we mean that there is not enough information for us to determine if the exploited vulnerability is related to a specific CVE or identifier,” Nathan Brubaker, senior manager for analysis at FireEye, told SecurityWeek. “This changes every day as information on the exploits and vulnerabilities are updated often. However, given the large proportion of the exploited vulnerabilities that fall into this category, and the age of some of the exploits, we don’t anticipate seeing the percentage of vulnerabilities that are potential zero days to change dramatically. We also note that while there may be associated CVEs in some cases that are simply not identified, it is very difficult for an asset owner to learn which vulnerabilities are or are not exploited by these modules.”
Learn More About ICS Security at SecurityWeek’s 2020 ICS Cyber Security Conference
A majority of the modules are developed for Core Impact and Immunity Canvas, which are both commercial products, unlike Metasploit, which is freely available.
In terms of the ICS products covered by these modules, many target Advantech, Schneider Electric, Siemens, Cogent, GE, and ICONICS.
Many of these ICS hacking tools have been developed by researchers and security practitioners, and they can be very useful for organizations looking to assess their security posture, but they can also make it easier for malicious actors to launch attacks on industrial systems.
“Although successful attacks against OT environments will normally require a high level of skills and expertise from threat actors, the tools and exploit modules discussed in this post are making it easier to bridge the knowledge gap,” FireEye said in a blog post.
The company added, “Awareness about the proliferation of ICS cyber operation tools should serve as an important risk indicator of the evolving threat landscape. These tools provide defenders with an opportunity to perform risk assessments in test environments and to leverage aggregated data to communicate and obtain support from company executives. Organizations that do not pay attention to available ICS cyber operation tools risk becoming low-hanging fruit for both sophisticated and unexperienced threat actors exploring new capabilities.”
Related: Dragos Acquires NexDefense, Releases Free ICS Assessment Tools
Related: GUI Now Available for Kamerka ICS/IoT Reconnaissance Tool
Related: Researcher Shows How Adversaries Can Gather Intel on U.S. Critical Infrastructure












