A graphical user interface (GUI) is now available for Kamerka, the open source reconnaissance tool that allows users to identify internet-exposed industrial control systems (ICS) and Internet of Things (IoT) devices.
Created by a researcher known as Wojciech, Kamerka’s first version was launched in November 2018. The tool was initially designed to identify nearby surveillance cameras that were accessible from the internet, but over the past year its developer has expanded its features and capabilities, and it can now be used to find a wide range of systems, including printers, ICS and IoT devices. The latest version adds support for several types of systems, including fuel tanks.
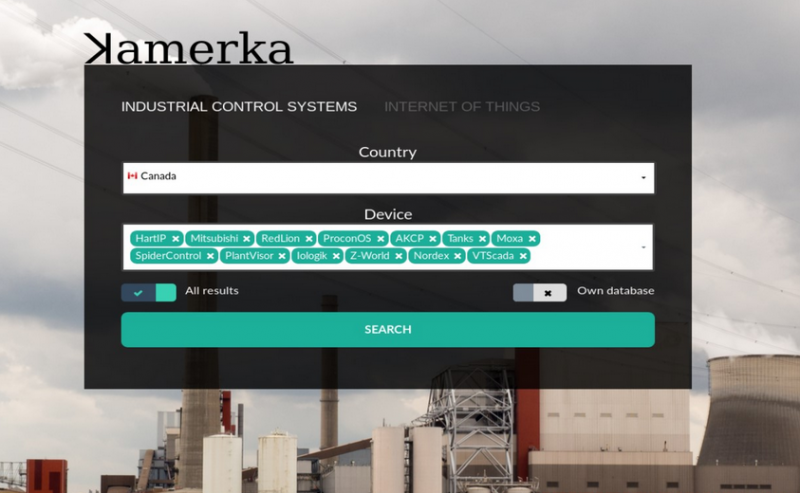
Until now, Kamerka could only be used through a command line interface (CLI), but Wojciech this week made available a browser-based GUI that makes it much easier to conduct searches. The web app was created with Django and it uses the default Django SQLite database.
Users who want to utilize Kamerka via its GUI need to set it up on a server. This can be done on a local server by installing Python3, Django, Redis, and the Celery task queue implementation for Python web apps — no special configuration changes are required for Kamerka to work. The tool also uses the Whois XML API, Shodan, BinaryEdge, Flickr and the Google Maps API to scan the web and manage the collected data.
The last step for setting up Kamerka on a local server involves running a few python commands, and the application will be available in the web browser on localhost on port 8000.
Learn More About Exposed ICS/IoT Systems at SecurityWeek’s 2020 ICS Cyber Security Conference
In the GUI, users can select the type of system — ICS or IoT — select a country or input geographical coordinates, and choose the type of device or protocol they are looking for. The tool then displays the results, which include the number of identified devices, ports, and some of the known vulnerabilities impacting the targeted systems. They can also view results on a map and use Google Street View to see the building housing an exposed device.
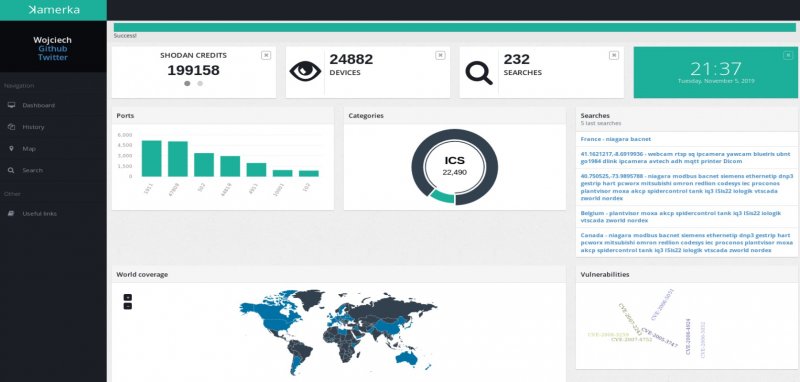
Wojciech recently demonstrated how Kamerka can be used to gather intelligence on critical infrastructure in the United States, and he provided additional examples in a blog post published on Wednesday.
The researcher believes the tool can be highly useful to local, state and federal government organizations for identifying critical infrastructure that may be exposed to malicious attacks.
Wojciech says he will continue to improve Kamerka. “I see a lot of possibilities for further development — more queries, integration with Nmap and PLCscan, offensive capabilities, more social media sources or automated separation of critical infrastructure from other devices,” he explained.
The complete source code for the Kamerka GUI is available on GitHub and the researcher has also set up a demo website.
Related: Tool Links Internet-Exposed ICS to Google Street View
Related: Intelligence Gathering on U.S. Critical Infrastructure
Related: Researcher Shows How Adversaries Can Gather Intel on U.S. Critical Infrastructure















