Cybercriminals have been using specially crafted URLs to trick even tech-savvy people into entering their Gmail credentials on a phishing website. Once an account has been compromised, the attackers immediately access it and start targeting the victim’s contacts.
The malicious emails come from one of the targeted user’s contacts and they appear to carry a PDF document that can be previewed directly from Gmail. However, clicking the “attachment,” which is actually an embedded image, takes the user to a Gmail phishing page.
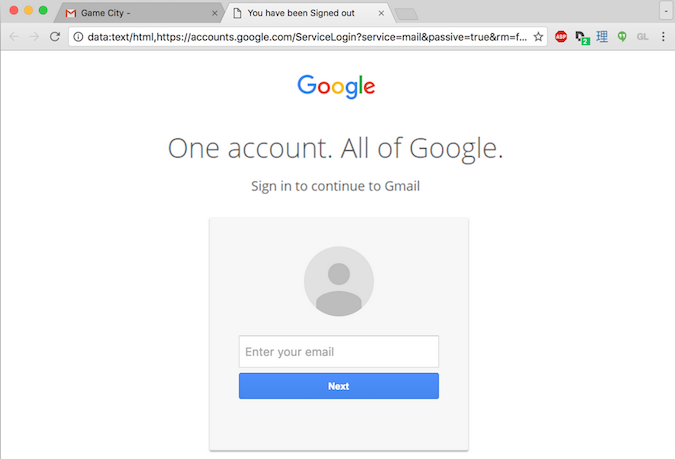
The URL of this phishing page starts with “data:text/html,https://accounts/google.com,” which could lead many users to believe the site is legitimate, especially since the web browser does not display any certificate warning.
The legitimate-looking part of the URL is followed by white spaces, which prevent the user from seeing any suspicious strings, and an obfuscated script that opens a Gmail phishing page in a new tab.
This method has been used for several months and even tech-savvy users have admitted taking the bait. In recent attacks, experts noticed that the cybercriminals immediately accessed the compromised accounts and used them to send out phishing emails to the victim’s contacts. It’s unclear if the process is automated or if the attackers are manually accessing the compromised accounts as soon as they obtain the credentials.
In one case, a school system administrator reported that the attackers turned legitimate messages from the victim’s inbox into phishing emails.
Enabling two-factor authentication (2FA) on Gmail should prevent phishers from accessing accounts once they’ve obtained the credentials. However, experts pointed out that if the attackers immediately access the compromised account, they could also phish the 2FA code.
A high-level analysis of these attacks was published last week by Mark Maunder, CEO and founder of WordPress security firm Wordfence. Maunder has warned that this technique, which appears to have a high success rate, can be used to steal credentials from many other platforms.
Google has been aware of these attacks since at least March 2016. A few days ago, the Chrome security team suggested introducing a “Not Secure” tag in the address bar for data:, blob: and other URLs that may be abused for phishing attacks.
Related Reading: Office 365 Business Users Targeted in Punycode-based Phishing
Related Reading: Spear Phishing Attacks Target Industrial Firms
Related Reading: Cybercriminals Use New Tricks in Phishing Attacks















