Many owners of My Book Live and My Book Live Duo network-attached storage (NAS) devices made by Western Digital (WD) reported having their files wiped, and it seems that it’s the result of an attack exploiting an old vulnerability.
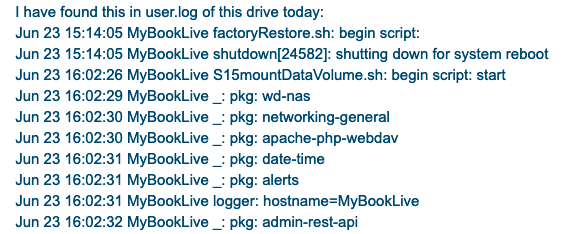
Victims said a factory reset had been initiated on their device, which resulted in all files being erased. Some users reported losing very important data.
 One post on the WD Community forum received more than 160 replies and it has been viewed nearly 15,000 times in just over 24 hours. A post on Reddit also received more than 80 responses within 24 hours.
One post on the WD Community forum received more than 160 replies and it has been viewed nearly 15,000 times in just over 24 hours. A post on Reddit also received more than 80 responses within 24 hours.
While some victims claim to have been able to recover some files using a tool named PhotoRec, currently there does not appear to be an easy way to recover files.
WD has launched an investigation and so far it hasn’t found any evidence to suggest that the incident is a result of a breach of its services or systems. The company says someone has been exploiting an old vulnerability to carry out the attack.
The flaw in question is CVE-2018-18472, which allows a remote attacker that knows the targeted device’s IP address to execute arbitrary commands with root privileges.
The statement issued by WD in response to the attacks suggests that not all hacked devices have been reset to factory settings.
The My Book Live and My Book Live Duo products are no longer supported. In fact, they haven’t received a firmware update since 2015, so it’s not surprising that they are still affected by a vulnerability discovered in 2018.
Until a better solution is identified, WD is advising owners of My Book Live devices to disconnect them from the internet.
Related: Western Digital Finds Replay Attack Protection Flaw Affecting Multiple Vendors
Related: QNAP Says Recently Patched Flaw Exploited in Qlocker Ransomware Attacks
Related: New Mirai Variant Delivered to Zyxel NAS Devices Via Recently Patched Flaw














