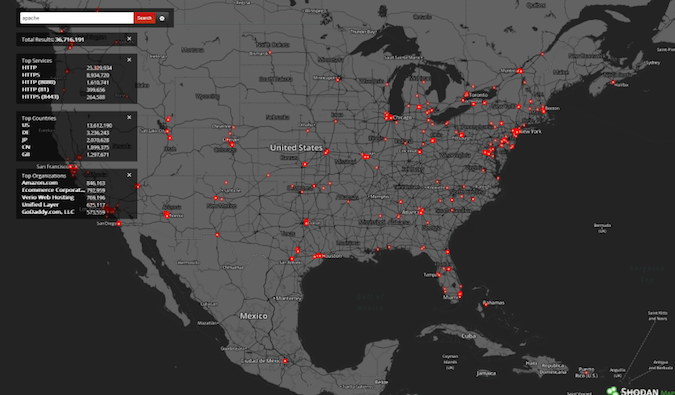
The popular IoT search engine Shodan this week announced the launch of Monitor, a new service designed to help organizations keep track of systems connected to the Internet.
Shodan Monitor allows organizations to gain full visibility into their Internet-exposed systems. Users can launch scans and configure real-time notifications in case a new device is detected.
According to Shodan, the new service is highly scalable, enabling users to monitor anywhere from one to millions of IP addresses. “The Shodan platform was built to handle networks of all sizes without breaking a sweat,” the company says.
Users can monitor not only devices on the local network, but all their connected systems. This can be highly useful for detecting exposed databases, phishing sites, and cloud data leaks.
Shodan Monitor is free for existing customers and its features are available via the Shodan API and the command-line interface.
Shodan pointed out that Chrome DevTools, a Google tool that can analyze runtime performance data, gave the new service a perfect score in terms of performance.
Related: Increasing Number of Industrial Systems Accessible From Web
Related: Refrigeration Systems Used by Supermarkets, Hospitals Left Exposed Online
Related: Hacker Search Engine Becomes the New Internet of Things Search Engine

