Over the last few years, business email compromise (BEC) scams have rocketed — costing victims $1.45 billion in 2016 alone (FBI report). Now a new related threat has emerged — the mortgage phishing scam — that seems likely to follow a similar trajectory.
It is early days and the scam — like BEC in its early days — goes by various names: mortgage phish, mortgage escrow scam, real estate wire transfer scam, and mortgage wiring scam. But it is growing. In June 2017, during National Homeownership Month, the FTC issued a warning: “the FTC and the National Association of Realtors want to remind you that scammers sometimes use emails to rob home buyers of their closing costs and personal information.”
Like BEC, the scam seeks to trick its victims into wiring funds to a criminally operated account. The difference here is that it people rather than businesses that are conned — and they can end up losing their life savings and/or their home.
The FTC warning explains the basic scam: “Hackers break into the email accounts of buyers or real estate professionals to get information about upcoming real estate transactions. The hacker then sends an email to the buyer, posing as the real estate professional or title company. The bogus email says there has been a last-minute change to the wiring instructions, and tells the buyer to wire closing costs to a different account. But it’s the scammer’s account. If the buyer takes the bait, their bank account could be cleared out in a matter of minutes.”
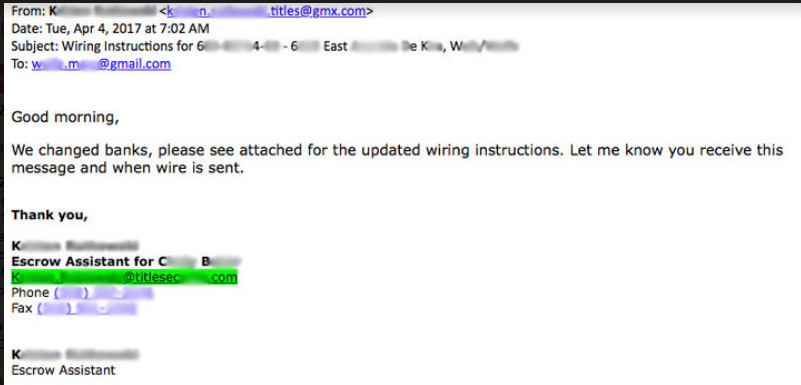
Barracuda Networks has described a real-life example that, in this instance, failed. “On the day that the buyers were set to wire funds, they received an email from their mortgage company stating that they switched banks, and to follow the updated wiring instructions in the email attachment.”
Home buyers are particularly vulnerable at this point. They may have spent many stressful months in arranging the purchase, and there is now one relatively simple task before they can collect the keys to their new home. In this instance, the scam failed. It raised a red flag for the buyer who looked more closely at the email — and noticed that the actual sender’s email address didn’t quite match the one listed in the real mortgage agent’s email signature.
The text of the email read, “We changed banks, please see the attached for the updated wiring instructions. Let me know you receive this message and when wire is sent.”
The attachment gives the attacker an extra shot at the target. If he opens the attachment but decides against making the wire, he could still find himself infected with a banking trojan or, potentially, ransomware. In this instance, however, the target did the right thing: he “immediately called his mortgage agent to confirm that the message was in fact a scam. What he found even more alarming with his situation,” adds Barracuda, “was the reaction that he received from the mortgage company. They mentioned that it’s a wide-spread problem, but they didn’t seem interested in looking into the issue any further.”
House prices have consistently grown since the 2006 crash, and now stand at similar or above their previous high. This makes it a lucrative market for scammers. “Scams like these have been around for a few years,” reported HousingWire in June this year.” Last year, the Contra Costa Association of Realtors warned Bay Area homebuyers that they could be targets of similar schemes, one of which cost a local buyer nearly $1 million.”
The mortgage phish is just another social engineering spear-phish; but the stakes are high and the targets are vulnerable. The Contra Costa Association warns, “Because buyers often put their complete faith in the real estate professionals who guide them through transactions, they very rarely challenge any advice and direction provided. Moreover, they are so comfortable making daily online transactions, they rarely, if ever question the authenticity of email or text messages.” It adds, “there is no means to retrieve the funds once wired.”
Last month Barracuda launched Sentinel, described as “an artificial intelligence (AI) powered spear-phishing and business email compromise (BEC) real-time detection and prevention solution.”















