The U.S. Department of Homeland Security (DHS) last year ordered government organizations to secure their email and web assets, but many agencies have failed to meet the deadline.
The Binding Operational Directive (BOD) 18-01, issued by the DHS on October 16, 2017, instructs federal agencies to start using web and email security technologies such as HTTPS, STARTTLS, SPF and DMARC. Agencies were given one year to set their DMARC policy to “reject,” which completely blocks the delivery of unauthenticated emails.
Several cybersecurity firms have been monitoring the progress, including Agari, Valimail and Proofpoint. They all found that while significant progress has been made, there are still many agencies that are not compliant one year after the directive was issued.
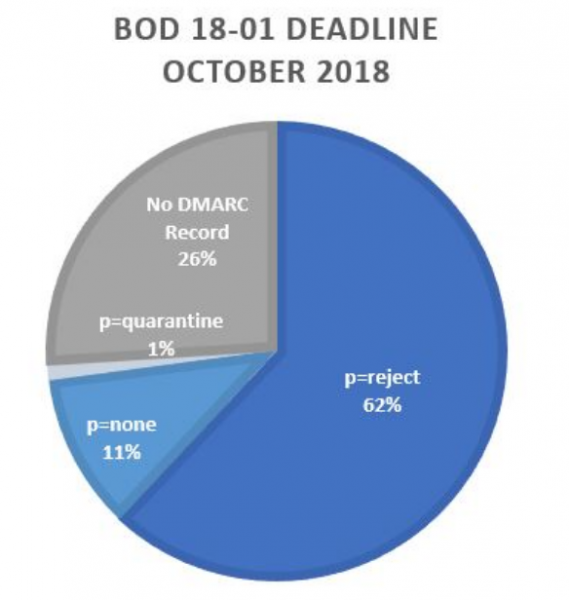
Agari has been monitoring 1,144 domains and found that 851 of them, representing 74%, have implemented DMARC with a “reject” policy as dictated by BOD 18-01. The company also pointed out that of the 278 domains with no policy or a “none” policy, only 28 are defensive domains (i.e. they don’t actively send email).
There are 46 executive branch agencies that have fully implemented DMARC, and 57 that either have no DMARC record or still have a “none” policy. A majority of the organizations that failed to become compliant only have one or two domains, Agari said.
“BOD 18-01 has clearly made a positive impact on the cybersecurity posture of the United States government,” commented Agari’s Fareed Bukhari. “It’s really great to see such a dramatic increase in adoption in such a short time frame. This is the fastest and most complete adoption of the DMARC standard for any industry in history. Private enterprise is definitely lagging behind the public sector now.”
Proofpoint has monitored 1,311 domains, including federal civilian domains, and its analysis also took into account the implementation of the Sender Policy Framework (SPF), which along with DomainKeys Identified Mail (DKIM) forms the foundation of DMARC. BOD 18-01 also requires the implementation of SPF.
Data collected by Proofpoint shows that over 60% of .gov domains are compliant with the BOD. Of all the organizations, 56% have implemented DMARC themselves and 21% have contracted the services of specialized providers.
“While not every agency is DMARC compliant with BOD 18-01 at the deadline, the progress made over the past year is commendable. Ideally, we will continue to see this positive trend until each agency fully protects their domains from email spoofing attacks. And while it is nice to see other industry groups taking a similar stance with DMARC authentication, BOD 18-01 has been a promising step in the right direction that organizations in all industries should follow,” explained Robert Holmes, vice president of Email Security at Proofpoint.
Valimail, which published its report one week before the deadline, noted that half of the 1,315 .gov domains it was monitoring had been compliant with BOD 18-01.
The company pointed out that 63 percent of compliant domains were not actually used for email. It also noted that DMARC records are not present on a vast majority of military domains, but these are not covered by the DHS directive, which exempts the Department of Defense, the intelligence community and national security systems.
Related: DMARC in Higher Education – A Formidable Defense Against Targeted Scams














