Long equipment life cycles and other factors expose manufacturing companies to a wide range of threats, according to a new report published on Wednesday by Trend Micro.
Manufacturing firms are increasingly relying on a combination of digital and physical systems to make production more efficient. However, the growing adoption of Industry 4.0 technologies and concepts, including industrial internet of things (IIoT), machine learning and big data, can also significantly increase an organization’s attack surface.
Using data from its Smart Protection Network infrastructure, Trend Micro has conducted a detailed analysis of the threats and risks impacting the manufacturing sector and drew comparisons to other industries.
Data collected by the cybersecurity firm between July and December 2018 showed that organizations in the manufacturing industry housed more devices running outdated operating systems compared to other sectors. For example, of a total of 150,000 machines used in manufacturing environments, nearly 5% had been running Windows XP, compared to less than 3% in other industries.
“This situation is most likely caused by a combination of a ‘do not touch a working system’ mentality and the long replacement cycle in hardware and software equipment. It is frequently seen in the manufacturing sector that the software components and drivers that support specialized equipment may not be compatible with more recent operating systems,” Trend Micro explained in its report.
“Because of the long life cycles of specialized equipment, the functional hardware may be considered obsolete by its vendor or may have reached end of support. In other cases, some systems or software may be left unsupported when a vendor merges with or acquires another vendor. In these instances, the software used to operate the hardware may no longer be supported, maintained, and updated, thus forcing equipment operators to use old operating systems to be able to continue running the equipment,” the company added.
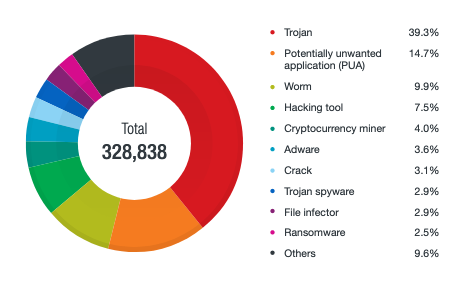
In terms of malware, the study found that worms, hacking tools, cryptocurrency miners, software cracks, file infectors and even ransomware are more commonly found in manufacturing organizations compared to other industries. Specifically, malware families such as WannaCry, Downad, AutoKMS, Coinminer and MalXMR are more common in this sector.
Downad, aka Conficker, is a worm that has been around for more than 10 years. It leverages an old Windows vulnerability, USB drives and network shares to spread. Downad and other pieces of malware that spread via USB often abuse autorun.inf files, which are used to automatically run applications on Windows.
Trend Micro says it has observed a significantly higher number of autorun.inf files in the manufacturing industry (25%), compared to the government (13%), education (12%), healthcare (11%), and technology (5%) sectors.
The manufacturing industry also accounts for the highest number of malicious CAD files detected by Trend Micro. Malware hidden in CAD files, which are normally associated with design software, can help attackers gain further access to compromised systems and conduct industrial espionage.
The manufacturing industry is exposed to both opportunistic and targeted attacks. One interesting targeted attack observed by the cybersecurity firm involved a Chinese manufacturing company hit by PlugX malware.
PlugX is typically used by Chinese threat actors and it’s rarely used in attacks targeting organizations located in China. PlugX is often used for industrial espionage, but in this case it had been used to deliver a piece of ransomware.
Trend Micro has also warned about the risks introduced by vulnerabilities in industrial control systems (ICS). Data from ICS-CERT showed that more than 120 vulnerabilities were found last year in manufacturing-related equipment and exploits are publicly available for many of these flaws.
Another problem are improperly configured systems that can be accessed remotely from the internet without any type of authentication.
Related: Energy Sector Most Impacted by ICS Flaws, Attacks
Related: SecurityWeek’s 2019 Singapore ICS Cyber Security Conference – Apr. 16-18













