Attackers increasingly targeted the country’s critical infrastructure such as power grids, water systems, and nuclear facilities in 2012, according to a recent Homeland Security report.
The department’s Industrial Control Systems-Cyber Emergency Response Team (ICS-CERT) responded to and investigated 198 cyber-incidents against critical infrastructure in fiscal year 2012, compared to 130 in 2011, according to the latest ICS-CERT Monitor report. The energy sector was the most targeted industry in 2012, accounting for 41 percent of reported events, followed by water with 15 percent.
This rise in attacks against critical infrastructure systems is hardly surprising given many of the headlines and reports that emerged during 2012.
 Other popular targets included commercial entities, government, transportation, and communications, according to the report. Chemical organizations reported seven incidents to ICS-CERT and nuclear plants reported six.
Other popular targets included commercial entities, government, transportation, and communications, according to the report. Chemical organizations reported seven incidents to ICS-CERT and nuclear plants reported six.
“Of the six incidents in the nuclear sector, ICS-CERT is not aware of any compromises into control networks,” the agency said in the report. The fiscal year in the report extends from Oct. 1, 2011 to Sept. 30, 2012.
The cyber-security response team helped with incident response and recovery for 23 oil/natural gas sector organizations after a targeted phishing campaign, the report said. ICS-CERT analyzed over 50 malware samples and malicious files, 20 emails, and 38 hard drive images to determine the extent of the compromise and to understand the techniques the attackers used. It turned out that in an incident, attackers successfully exfiltrated information pertaining to an industrial control systems and SCADA environment, including how to remotely operate the systems.
Spear phishing and Internet-facing systems with weak or default credentials were the most common incidents in the water sector.
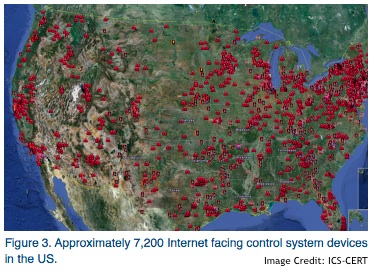 In fact, control systems devices that could be directly accessed from the Internet were an “area of concern” in fiscal year 2012, ICS-CERT said. Researcher Eireann Leverett used the SHODAN search engine to identify and locate 20,000 ICS-related devices that could directly be addressed over the Internet and had weak or default authentication, according to the report.
In fact, control systems devices that could be directly accessed from the Internet were an “area of concern” in fiscal year 2012, ICS-CERT said. Researcher Eireann Leverett used the SHODAN search engine to identify and locate 20,000 ICS-related devices that could directly be addressed over the Internet and had weak or default authentication, according to the report.
“A large portion of the Internet-facing devices belonged to state and local government organizations,” ICS-CERT said. Along with incident response, ICS-CERT also coordinates vulnerability disclosures between researchers, vendors, and the industry. ICS-CERT tracked 171 unique vulnerabilities affecting ICS products across 55 different vendors in fiscal year 2012, compared to 145 vulnerabilities tracked in 2011. While the total number of vulnerabilities increased from a year ago, buffer overflows still remained as the most common vulnerability type, the report said. The good news is that buffer overflow issues accounted for only 26 percent of reported vulnerabilities, compared to 46 percent in 2011.
More than 24 types of vulnerabilities were reported, including input validation, cross-site scripting, resource management, access control, hard-coded credentials, encryption issues, and SQL injection.
“ICS-CERT also noted an increase in vulnerabilities related to hardware, including ICS networking and medical devices,” the report said.
The report described two separate incidents at a power generation company and an electronic utility where an infected USB drive infected several computers on the network. In both cases, having an antivirus product with up-to-date definitions would have been effective in detecting and blocking the malware from infecting the machines. ICS-CERT recommends owners and operators of critical infrastructure should also have policies in place governing the use of removable media, such as regularly scanning and cleaning all removable media so that they can’t infect multiple systems.
“Such practices will mitigate many issues that could lead to extended system downtimes,” ICS-CERT said.
ICS-CERT also reminded readers about the benefits of continuous monitoring and that help is available for organizations looking to implement continuous monitoring.
As SecurityWeek columnist Dr. Mike Lloyd of RedSeal Networks recently noted, an audit once a year is all pain for very little gain, while continuous monitoring “isn’t just more of the same – it’s a real transformation of the objective and the outcome.”













