Santa Doesn’t Care if You Were Naughty or Nice on Christmas Eve – What Matters is How you Did all Year. Security is Much the Same.
Whether you think continuous monitoring was the theme of security in 2012 may depend on whether you live inside or outside the DC Beltway. If you’re working on security for or on behalf of a Federal agency, you probably don’t need me to explain what continuous monitoring means. If you don’t, then you may not know yet how badly you need to know, but that’s OK – you can thank me later!
No matter where you do your time in the security trenches, you know we’re losing this war. And let’s face it – we’re all in the trenches now, right up to the generals. No hiding behind the lines in these days when a pre-pubescent kid in Eastern Europe or a nation state can equally decide you look like the next good target. The question is how we should fix it.
 We’ve tried buying tons of technology – every latest sure-fire cure-all. Somehow even the great and mighty still get taken down. Why? In one word: complexity. The Verizon Data Breach Investigation Report makes it quite clear – 97 percent of real breaches could be prevented through “consistent application of simple or intermediate controls”. We know how to defend ourselves – we’re just not doing it consistently. Attackers are winning with easy exploits because they can – they don’t have to use elaborate, expensive zero-day exploits when we always end up leaving a side door open. The problem is there are just so very many side doors – we can’t even check the basics, in networks of the size we use today. Unfortunately, Santa probably isn’t going to magically grant you:
We’ve tried buying tons of technology – every latest sure-fire cure-all. Somehow even the great and mighty still get taken down. Why? In one word: complexity. The Verizon Data Breach Investigation Report makes it quite clear – 97 percent of real breaches could be prevented through “consistent application of simple or intermediate controls”. We know how to defend ourselves – we’re just not doing it consistently. Attackers are winning with easy exploits because they can – they don’t have to use elaborate, expensive zero-day exploits when we always end up leaving a side door open. The problem is there are just so very many side doors – we can’t even check the basics, in networks of the size we use today. Unfortunately, Santa probably isn’t going to magically grant you:
• Tighter risk control
• Better network assurance
• An effective security posture
• Reduced operations & compliance costs
• Increased operational efficiency
So what’s the answer? It’s an old answer – vigilance. If we could simply check the basics, thoroughly, pervasively, we’d be far, far harder targets than we are today. The bad guys know it – all they need are automated search tools, and they are pretty much sure to find a corner you missed, because you aren’t as automated as they are. (They also only need to find one way in – you have to block all of them. Nobody said this game was fair.)
This brings us back to continuous monitoring. We’ve tried not-so continuous – we call that “audit.” In a seasonal theme, Santa doesn’t care if you were naughty or nice on Christmas Eve – what matters is how you did all year. Security is much the same. For all that you try, you can’t fix it all in a mad scramble ahead of audit day. It didn’t work when we were four, and it doesn’t work now.
And this is the message that’s emanating from the winter wonderland of DC – “continuous monitoring” means “get in control, test your controls, prove your controls, and show you are doing this ALL the time.” The only way to do this is to automate. Attackers already do it; the defenders have no choice now. And for Federal agencies, even if you don’t want to, FISMA regulations now demand it. (It’s not just a good idea – it’s the law.) How will this affect you if you’re not in government?
First, regulations for Federal agencies rapidly extend to suppliers to Federal agencies and that almost certainly means you too. (Where do you think your equal employment or drug policies came from? Enlightened good will? In a few cases, maybe.) Second, it’s also a very good idea.
Audit once a year is all pain for very little gain – the report’s already out of date with dynamic reality by the time the toner’s dry.
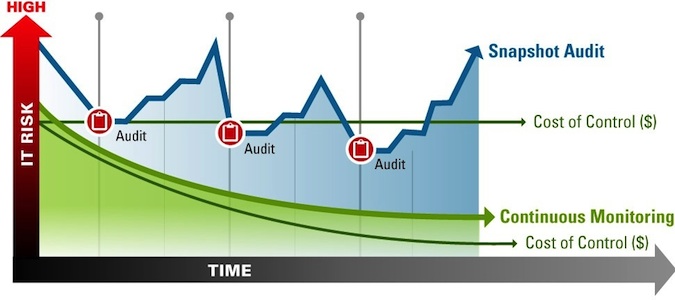 Continuous monitoring isn’t just more of the same – it’s a real transformation of the objective and the outcome. Automation means less pain and when we’re suffering real breaches due to occasional lapses of known controls, we know we need computers. They may not be smart, but they sure are diligent. I use machine assessment of security every day – I help organizations achieve that light bulb moment of “my goodness, I had no idea” when we turn up obvious errors in their IT infrastructure. Everybody wins (except the bad guys) when we can find and fix the flaws that are allowing the real breaches, but that are hidden in the forests of complexity we live with.
Continuous monitoring isn’t just more of the same – it’s a real transformation of the objective and the outcome. Automation means less pain and when we’re suffering real breaches due to occasional lapses of known controls, we know we need computers. They may not be smart, but they sure are diligent. I use machine assessment of security every day – I help organizations achieve that light bulb moment of “my goodness, I had no idea” when we turn up obvious errors in their IT infrastructure. Everybody wins (except the bad guys) when we can find and fix the flaws that are allowing the real breaches, but that are hidden in the forests of complexity we live with.
So don’t try to fool your auditor – these days, you can automate IT control assessment to the point where you save money while making your network safer. (And you can avoid that lump of coal in your stocking.)
Here’s wishing you a Happy Holiday Season and a Very Nice New Year!

