The GozNym banking Trojan has been observed targeting the customers of some of the largest financial institutions in the United States, IBM Security warned on Wednesday.
GozNym, a hybrid between the Nymaim dropper and the Gozi ISFB financial malware, was first spotted by IBM X-Force researchers in early April. When it emerged, the Trojan had been spotted targeting banks in North America. Experts later reported that cybercriminals started launching redirection attacks against 17 banks in Poland and one major bank in Portugal.
IBM Security now says malicious actors have started leveraging redirection attacks to target four of the largest banks in the United States, focusing on business banking services customers.
In a redirection attack, the malware hijacks the victim’s browsing session and takes them to a fake website that looks exactly like the legitimate site. On these phishing sites, victims are instructed to provide personal and financial information that cybercriminals can use to conduct fraud.
In GozNym’s case, the redirection attacks are designed to trick both users and security researchers. The fake bank webpages are made to look like they are hosted on the targeted organization’s genuine URL and they even display the SSL certificate in the browser’s address bar.
The redirection attacks have two phases. First, the malware redirects the user to the phishing page and masks the page with a white overlay screen. Then, the overlay is removed and the fake website is revealed. By using the overlay screen, attackers make it look like an empty page in case researchers try to examine it.
“Redirection attacks are not considered to be a technically complicated task, but they are clever and require ample resources to set up. This is also why redirection attacks are not deployed by all financial malware operators; rather, they are the domain of organized cybercrime,” explained Limor Kessem, executive security advisor at IBM. “Redirection attacks are often associated with the resources and capabilities of organized cybergangs that have developers on the team because extra setup and site maintenance is required to pull it off.”
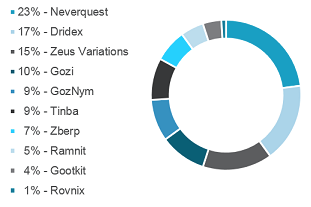
According to IBM, GozNym was the fifth most aggressive malware by attack volume in the first half of 2016, and it could continue to climb as the number of banks it targets via redirection attacks grows. In the case of Dridex and Dyre, redirection capabilities helped them become some of the most aggressive banking Trojans.