Google security researchers revealed that two of the vulnerabilities patched by Apple on Thursday with the release of iOS 12.1.4 were zero-day flaws exploited in the wild by malicious actors.
iOS 12.1.4 resolves a total of four vulnerabilities. Two are related to the recently discovered FaceTime spying bug, and the other two are memory corruption issues that allow a malicious application to elevate privileges and execute arbitrary code.
One of the flaws, tracked as CVE-2019-7286, impacts the Foundation component in iOS and it allows a malicious application to gain elevated privileges. The second vulnerability, identified as CVE-2019-7287, impacts IOKit and it can be exploited by a malicious app to execute arbitrary code with kernel privileges.
Apple has credited Clement Lecigne of Google Threat Analysis Group, along with Ian Beer and Samuel Groß of Google Project Zero for reporting these issues. An anonymous researcher has also been credited by the tech giant.
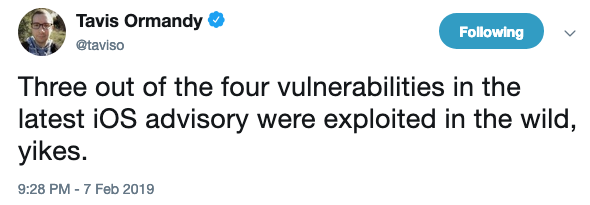
Project Zero Team Lead Ben Hawkes revealed on Twitter that both CVE-2019-7286 and CVE-2019-7287 have been exploited in the wild, but no details have been shared about the vulnerabilities or the attacks.
It’s worth noting that CVE-2019-7286 has also been patched in macOS Mojave with the release of a supplemental update for version 10.14.3, which also resolves the Facetime-related issues.
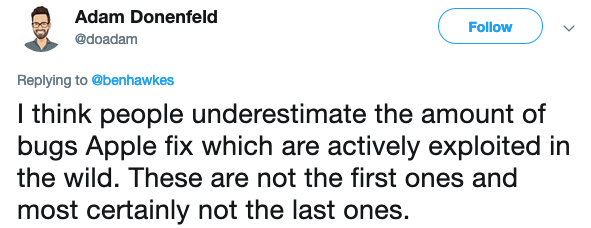
While it may seem that iOS and macOS vulnerabilities are rarely exploited in attacks, some experts warn that it’s actually not that uncommon.
Apple has also released an update for Shortcuts for iOS to address a local information disclosure flaw and a sandbox bypass issue.
Related: Apple Patches Dozens of Vulnerabilities in iOS, macOS
Related: Apple Patches Tens of Flaws in iOS, macOS, Safari
Related: iOS 12 Brings Patches for 16 Security Vulnerabilities













