Google’s G Suite team announced on Wednesday that, for security reasons, Gmail will soon stop allowing users to attach JavaScript (.js) files to emails.
Currently, there are more than two dozen potentially dangerous file types that can’t be used as attachments in Gmail, including .exe, .jar, .sys, .scr, .bat, .com, .vbs and .cmd. Starting on February 13, 2017, .js files will also be added to the list.
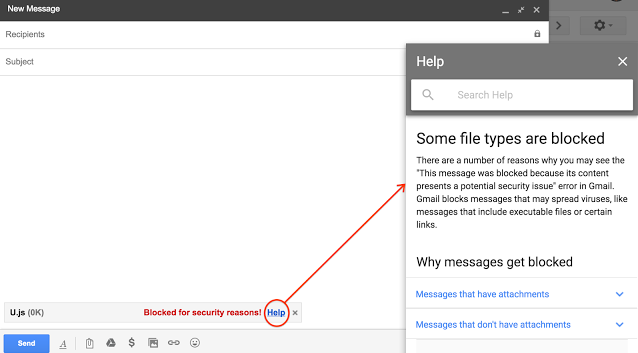
Users who attempt to attach these types of files will see a message informing them that the file has been blocked for security reasons. A “Help” link will be provided for people who may want additional information.
For cases where users need to send .js files for legitimate reasons, Google recommends using Drive, Cloud Storage or other file-sharing services.
There have been several campaigns recently where attackers delivered malware by attaching JavaScript files to emails. For instance, the cybercriminals behind the Locky ransomware used JavaScript attachments to drop downloaders, and they later started directly embedding the malicious binary into the JavaScript file.
Ransomware has been increasingly using JavaScript (e.g. Ransom32, RAA) and significant spam campaigns delivering malicious .js files are not uncommon, which is probably why Google has decided to block these types of files.
Google made several security improvements to Gmail in the past year: it enhanced security alerts, it started flagging unauthenticated messages and potentially dangerous URLs, and it disabled support for the RC4 cipher and the SSLv3 protocol.
Related: Google’s DLP for Gmail Adds Optical Character Recognition
Related: Phished Gmail Accounts Immediately Accessed by Hackers

