The U.S. Central Intelligence Agency (CIA) has developed a tool that disables security cameras and corrupts recordings in an effort to prevent its agents from getting compromised, according to documents published on Thursday by WikiLeaks.
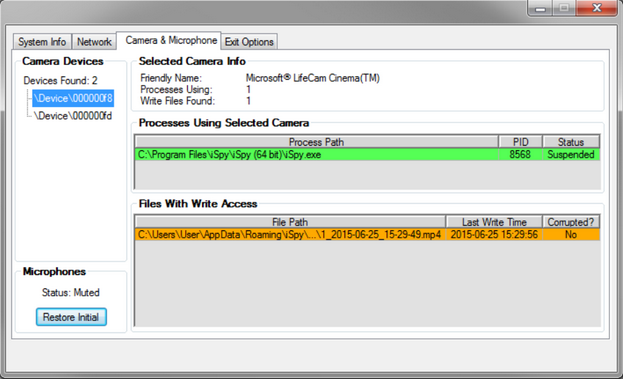
The tool, dubbed “Dumbo,” is executed directly from a USB thumb drive by an operative who has physical access to the targeted device. Once executed, the program can mute microphones, disable network adapters, and suspend processes associated with video recording devices.
Dumbo also informs its user of where those video recording processes store footage so that the files can be corrupted or deleted.
The user guides made available by WikiLeaks — the latest version is dated June 2015 — show that the tool was developed in response to the need for a capability to disrupt webcams and corrupt recordings in an effort to prevent a PAG (Physical Access Group) deployment from getting compromised.
PAG is a special branch within the CIA’s Center for Cyber Intelligence (CCI) and its role is to gain physical access to computers and exploit this access, WikiLeaks said.
The tool, designed for Windows XP and newer versions of the Microsoft operating system, needs SYSTEM privileges to function correctly.
“[The tool] identifies installed devices like webcams and microphones, either locally or connected by wireless (Bluetooth, WiFi) or wired networks. All processes related to the detected devices (usually recording, monitoring or detection of video/audio/network streams) are also identified and can be stopped by the operator,” WikiLeaks said. “By deleting or manipulating recordings the operator is aided in creating fake or destroying actual evidence of the intrusion operation.”
Dumbo developers pointed out that home security products (e.g. Kaspersky antivirus) may block some of the tool’s functions, and advised users to disable any protections before installation.
WikiLeaks has exposed numerous tools allegedly used by the CIA as part of a leak dubbed Vault 7. The tools detailed so far are designed for hacking Mac OS X devices (Imperial), intercepting SMS messages on Android devices (HighRise), redirecting traffic on Linux systems (OutlawCountry), stealing SSH credentials (BothanSpy), spreading malware on an organization’s network (Pandemic), locating people via their device’s Wi-Fi (Elsa), hacking routers and access points (Cherry Blossom), and accessing air-gapped networks (Brutal Kangaroo).
Related: Cisco Finds Zero-Day Vulnerability in ‘Vault 7’ Leak












