A remotely exploitable vulnerability in the Cisco Emergency Responder software could allow an unauthenticated attacker to log in to an affected device using the root account, according to a warning from the U.S. tech vendor.
The vulnerability, tracked as CVE-2023-20101, carries a CVSS severity score of 9.8/10 and a “critical” tag from Cisco’s security response team.
From the Cisco advisory:
“A vulnerability in Cisco Emergency Responder could allow an unauthenticated, remote attacker to log in to an affected device using the root account, which has default, static credentials that cannot be changed or deleted.”
“This vulnerability is due to the presence of static user credentials for the root account that are typically reserved for use during development. An attacker could exploit this vulnerability by using the account to log in to an affected system. A successful exploit could allow the attacker to log in to the affected system and execute arbitrary commands as the root user.”
Cisco said the security defect affects only Cisco Emergency Responder Release 12.5(1)SU4.
The San Jose, Calif. company is urging Cisco Emergency Responder users to immediately apply the available patches, warning that there are no workarounds that address this vulnerability.
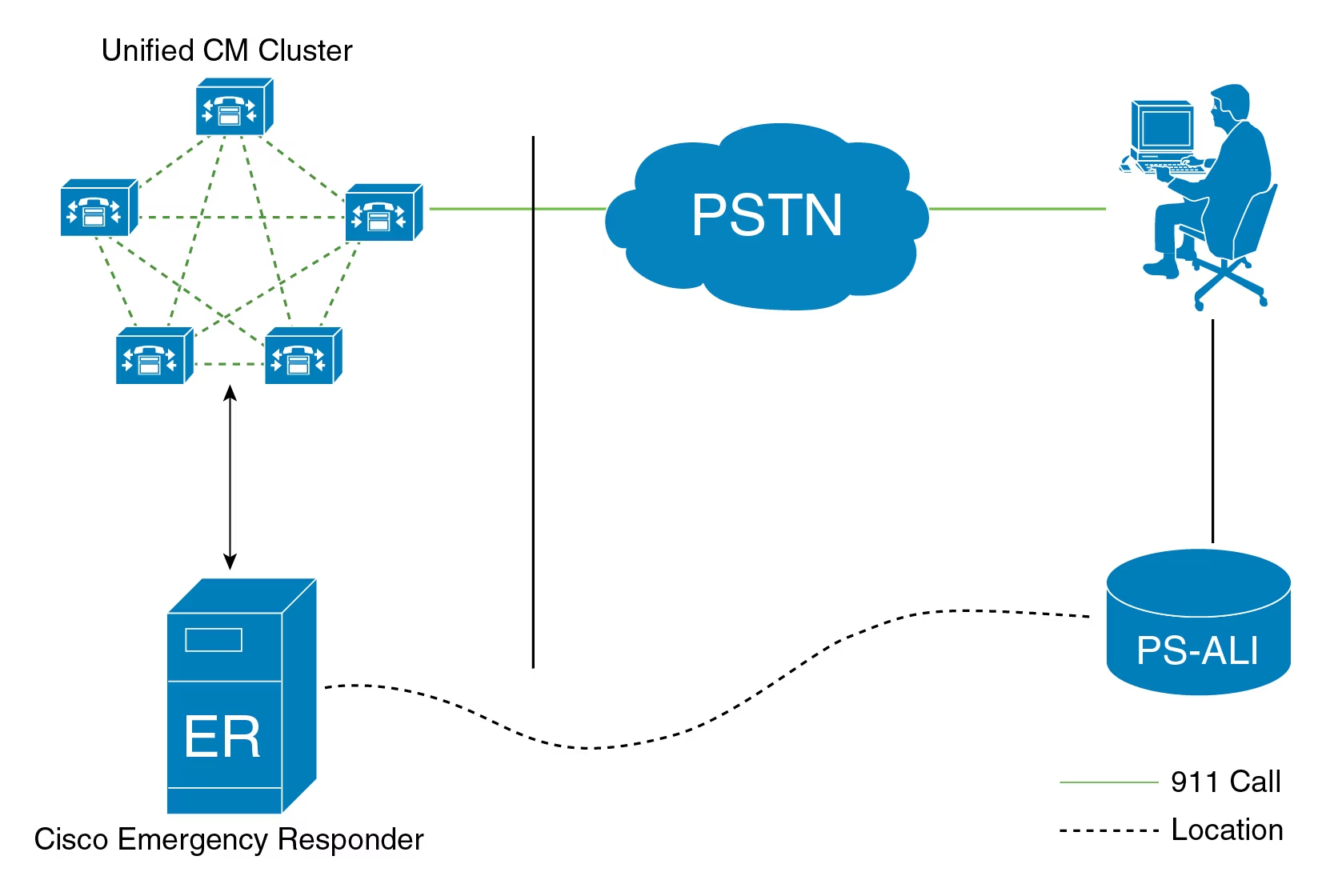
The Cisco Emergency Responder software works in tandem with the Cisco Unified Communications Manager to send emergency calls to the appropriate Public Safety Answering Point (PSAP) for a caller’s location.
Available in the US and Canadian markets, the software is used to route emergency calls to a local public-safety answering point (PSAP), alert personnel by email or phone of an emergency call to respond to locally, keep logs of all emergency calls and provide the PSAP with accurate geolocation of the caller in need.
Related: Chinese Gov Hackers Caught Hiding in Cisco Router Firmware
Related: Cisco Warns of WebEx Player Security Vulnerabilities
Related: Live Exploits Underscore Urgency to Patch WS-FTP Server Flaw
Related: US Gov Warning: Firmware Security a ‘Single Point of Failure’